March 26, 2026 · by Synoptek Team 5 min read
As cyber threats evolve and the regulatory environment advances, organizations are under increasing pressure to demonstrate that their security posture is not only effective but also defensible.
Frameworks like the NIST Cybersecurity Framework have become the standard for evaluating and improving security maturity. Yet many organizations struggle with a fundamental question:
How do you actually use NIST to understand where you stand, and what to do next?
This blog explains what the NIST Cybersecurity Framework is, why it matters, and how you can use it to benchmark your security maturity in a practical and actionable way.
What is the NIST Cybersecurity Framework?
The NIST Cybersecurity Framework (CSF) is a widely adopted set of guidelines designed to help organizations manage and reduce cybersecurity risk.
Developed by the National Institute of Standards and Technology, it provides a structured approach to:
- Identifying security risks
- Protecting critical systems and data
- Detecting and responding to threats
- Recovering from security incidents
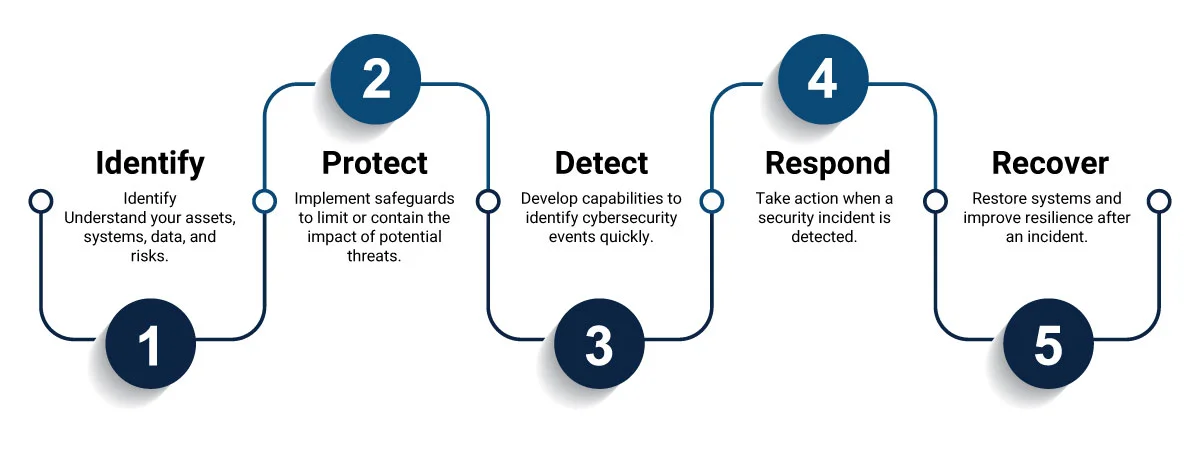
At its core, the framework is built around five key functions:
While the framework is straightforward in theory, applying it across modern environments, especially those spanning identity, cloud, and endpoints, is where complexity begins.
Why the NIST Cybersecurity Framework Matters Today
Security today is no longer just about perimeter defense; it’s about identity, access, and control across distributed environments.
Organizations face increasing challenges:
- Identity-driven attacks and privilege misuse
- Misconfigured cloud environments (Azure, Microsoft 365)
- Inconsistent enforcement of security controls
- Rising audit and compliance expectations (SOC 2, ISO 27001, HIPAA)
- Pressure from boards, regulators, and investors
Many organizations rely on tools, dashboards, or scores to measure security. But these often provide a fragmented view, leaving critical gaps hidden until:
- An audit exposes them
- A breach occurs
- A due diligence process uncovers risk
The NIST Cybersecurity Framework helps shift from tool-based visibility to structured, framework-aligned maturity.
What is Cybersecurity Maturity and Why Does It Matter?
Cybersecurity maturity refers to how consistently and effectively your organization implements and enforces security controls.
It helps answer crucial questions:
- Are controls enforced across all users and systems?
- Are policies consistently applied across cloud and endpoints?
- Can you prove your security posture to auditors or stakeholders?
- Do you know which risks matter most to fix first?
Without a clear maturity baseline, organizations operate reactively, addressing issues only when they become visible.
How to Benchmark Your Security Maturity Using NIST
Benchmarking your security maturity against the NIST Cybersecurity Framework requires a structured, evidence-based evaluation across key control areas.
Here’s how leading organizations approach it:
1. Establish a Baseline
Start by evaluating your current state across identity, cloud governance, and endpoint security.
This includes:
- MFA enforcement and access controls
- Privileged role management
- Cloud configuration and governance (Azure/M365)
- Endpoint security and device compliance
2. Map to NIST Functions
Align your findings to the five NIST functions (Identify, Protect, Detect, Respond, Recover).
This helps translate technical gaps into framework-aligned insights that leadership and auditors understand.
3. Identify Gaps and Risks
Not all gaps are equal. The goal is to uncover:
- High-risk misconfigurations
- Areas of inconsistent enforcement
- Identity and access vulnerabilities
- Cloud governance gaps
4. Prioritize Based on Risk
Instead of fixing everything at once, prioritize based on:
- Business impact
- Likelihood of exploitation
- Exposure to ransomware or identity-based attacks
5. Build a Remediation Roadmap
Translate findings into a clear, prioritized action plan that can be executed by IT and security teams.
Why Most Organizations Struggle with NIST Implementation
While the framework is powerful, many organizations struggle to operationalize it because:
- They lack visibility across identity, cloud, and endpoints
- Security ownership is fragmented across teams
- Tools don’t provide a unified view of maturity
- There’s no clear way to prioritize what matters most
As a result, NIST becomes a compliance exercise rather than a strategic tool for improving security posture.
Moving from Secure Score to Security Maturity
Many organizations rely on tools like Microsoft Secure Score to evaluate security. While useful, these scores often:
- Focus on configurations, not real risk
- Don’t account for enforcement consistency
- Lack business context
To truly benchmark maturity, organizations need a framework-aligned, evidence-based assessment.
This is where a structured approach, like a Security Assessment, comes in.
How a Security Assessment Helps You Benchmark Maturity
A focused 3–5 week Security Assessment provides:
- A clear, defensible security maturity baseline
- Benchmarking against frameworks like NIST, SOC 2, and ISO 27001
- Visibility into gaps across identity, cloud, and endpoints
- Risk-ranked findings (High / Medium / Low)
- A prioritized remediation roadmap
Instead of guessing where you stand, you gain clarity, alignment, and a path forward.
Learn How to Identify Your Security Gaps
If you’re preparing for an audit, transaction, or simply want to understand your true security maturity, the first step is visibility.
Final Thoughts
The NIST Cybersecurity Framework is more than a compliance tool; it’s a foundation for building a measurable, defensible security posture.
But the real value comes from how you apply it.
Organizations that move beyond fragmented tools and adopt a structured, framework-aligned approach gain:
- Clear visibility into security maturity
- Confidence in audit and compliance readiness
- Reduced exposure to modern threats
- A practical roadmap for continuous improvement
The question isn’t whether you should use NIST; it’s whether you truly know where you stand.

