What are the Top Benefits of Dynamics CRM?
There are many CRM packages in the market, but how do you know if Dynamics 365 is the best choice for your business? To help you decide, here is a list of Dynamics CRM's key benefits:- Prioritizing and nurturing the right leads
- Predicting future sales and budgets
- Streamlining the sales process
- Centralizing customer data
- Getting insights into your customers' journey
- Offering customers an easy-to-use, self-service portal
- Providing customizable dashboards
- Integrating easily with other software solutions
- Connecting with buyers on their preferred channels
Why Should you Consider Synoptek for Your Dynamics CRM Needs?
As a Microsoft Gold Partner, Synoptek employs best practices to understand your specific business requirements and then design the Dynamics CRM solution to perfectly meet all your needs. We assist you in utilizing the full potential of your Dynamics CRM software to provide you with a 360-degree perspective of your customers, which can help you improve your lead conversion rates, generate revenues from existing customers, and support excellent customer service initiatives. We provide the following Dynamics 365 CRM services to help you grow your business:- Business Consulting, Advisory, and Planning
- Full Cycle Implementation
- Customization and Technical Advisory
- Application Integration
- Dynamics CRM Migration, Upgrade, and Optimization
- Support and Maintenance
- License Optimization and Negotiation
What is CRM Consulting?
CRM Consulting involves leveraging the expertise of competent professionals to exploit the capabilities of a modern CRM platform to the fullest. By understanding the journey of your business and the story of your customers, CRM Consulting helps in building a custom solution and shifting your legacy systems and processes to a digital infrastructure that encompasses the entire organization. CRM Consulting enables organizations to plan the best strategy for sales, marketing, and customer support activities while achieving the highest ROI from any CRM implementation. By getting access to qualified and certified CRM consultants, they can identify current gaps, chart out a robust plan, and implement processes to meet diverse business needs via tailored CRM solutions.Why Do You Need a CRM Consultant?
Understanding the needs of customers and offering them products and services that align with those needs is critical. A CRM does the perfect job of uncovering these facets using data insights; but being able to unearth these insights requires the constant oversight of skilled professionals who can help in providing personalized communication, sharing relevant information, and delivering consistent service. If you are unaware of the different CRM solutions available in the market, lack a good understanding of the CRM implementation process, or do not have the time or resources for strategic execution and maintenance of CRM software, you need a CRM Consultant to help you achieve all this, and more. Having a CRM Consultant on board can help your business effectively manage all customer-related activities through the successful selection, implementation, and optimization of a CRM platform that perfectly fits your business requirement. Offering functional and technical expertise, a CRM Consultant can conduct technical analysis of your CRM requirements, craft the right functional specifications, customize modules as needed, and keep the CRM solution in line with your needs. A Consultant can also help in configuring, deploying, and integrating the solution as well as supporting and managing it post-implementation, and training users to leverage the system most efficiently.What are the Benefits of CRM Consulting?
CRM Consultants provide a vast scope of CRM Consulting Services, starting from defining the industry and client-specific business processes, collecting business requirements, supporting the CRM vision, building an implementation roadmap, and configuring and customizing the CRM solution. Companies that opt for CRM Consulting can achieve several benefits, such as:- Successful implementation and management of the CRM platform
- Stronger sales pipeline
- Better workforce productivity through automation
- Improved customer satisfaction and retention
- Reduced operating costs
- Continuous updates and upgrades of the CRM platform
- Increased flexibility and scalability
- 24/7 availability
Reasons Why You Need to Invest in a CRM
A great CRM helps a company analyze and manage its interactions with old and new customers. CRM stands for customer relationship management, without it, organizations fall behind on potential revenue and the ability to streamline most of the interactions with new customers. It is no secret that the best way to achieve exponential growth with your business is by consistent management that monitors and comprehends its data.How Can You Choose the Right CRM Consultant?
Choosing the right CRM Consulting Partner that has certified resources and is partners with CRM vendors like Microsoft, Salesforce, and SAP requires you to look out for certain skills and capabilities. These include:- A pool of qualified and certified resources with expertise in multiple CRM platforms
- Years of experience in the field of CRM Consulting and a track record of successfully completed projects
- A global delivery model to meet unique business requirements, regardless of time-zone differences
- CRM product development expertise along with migration and integration capabilities
- Robust discovery and implementation processes and knowledge of the latest CRM trends and best practices
- Proven quality control and assurance tools and processes
- Sufficient industry and domain expertise
- Sound SLAs and a service desk where issues can be logged 24x7
- Good references from current and past customers
The Advantages of a Mobile CRM
Mobile has completely changed the way we do business in this day in age, it has forced the entire world to make information accessible to everybody with the touch of a button. Mobile CRM is no longer an option, but a need. Now you can approve requests, Access real-time dashboards, create custom reports and share ideas and reports. With Dynamics CRM, your organization can do everything you would normally be able to do from a desktop application, on the go.Investing in CRM with Synoptek
If you want to efficiently forge and manage customer relationships, track sales leads, and build a strong sales and marketing pipeline, investing in a CRM platform is a great way to streamline your administrative processes and increase your profitability. But given how multifaceted today’s CRM platforms are, CRM Consulting can allow qualified experts to take care of all things CRM while you focus on building and maintaining customer relationships that truly matter. Invest in a CRM Consultant today to optimize your sales processes and never miss out on a growth opportunity, ever!- Automate as much as possible.
- Ensure top-notch security throughout the process.
- Ensure collaboration across the engineering as well as the business teams.
- Provide the best tools and set the best processes for the team.
- Set the right expectations in terms of quality and timeline.
- Keep all versions organized.
- Always test the scalability of the final product.
- Partner with an experienced firm with relevant software development experience.
How Synoptek Can Support Your Business Application Development Strategy
Synoptek has a highly experienced Product Development team. We can turn your ideas into a robust, efficient product. Whether you need bespoke software, development support service, or end-to-end business application development, Synoptek’s innovative software development services can deliver to your vision. Our team has a deep understanding of the adoption of Business Application platforms across industries such as financial services, manufacturing, healthcare, telecommunications, pharmaceuticals, and technology, as well as public sector institutions such as governments and universities. Our technical professionals also come with a deep understanding of specialized applications such as ERP, CRM, and e-commerce platforms. With our thorough expertise in product development and our cross-industry experience with Business Applications, we can guarantee the delivery of the highest quality software at all times, under the toughest of circumstances. By partnering with our team, you can not only accelerate time-to-market by reducing time spent across all stages of the application development lifecycle through automation but also experience seamless product delivery. As our experienced DevOps team is closely involved with the Business Applications development projects, you will be able to see continuous improvements in your products through smooth, well-executed, timely sprints. With the Business Applications developed by our team, you will achieve:- Higher and faster value for your business
- Technological excellence
- Value for money
Hyperscale Cloud Computing at Synoptek
When it comes to making cloud-based IT infrastructure, migration is only half the battle. The infrastructure must adapt as a firm develops and develops, and that is why the ability to hyperscale becomes crucial. Synoptek's hyperscale services help enterprises with IT infrastructure design and management facilitate suitable and continuous scaling as demands arise. Through our hyperscale (managed cloud services), we also provide a layer of risk management, data protection, security services, and long-term strategic planning to Amazon Web Services (AWS) and Microsoft Azure. If a business has current cloud resources that simply aren't working as expected, it can leverage Synoptek's hyperscale cloud services.Why is Cloud Infrastructure Optimization Important?
Cloud optimization helps evaluate an organization’s workload patterns, including use, history, and operational costs. It then assists in combining this information with the knowledge of available cloud services and configurations to provide recommendations that help improve workload-to-service matching. Investing in managed cloud services is the best way to optimize an organization’s cloud infrastructure. Not only can partnering with the right managed service provider (MSP) help the enterprise keep their infrastructure secure, but it will also help them optimize spend and time and allow them to focus more on operational outcomes.How to Implement Cloud Infrastructure Optimizations?
Businesses must take the following steps to understand, measure, and optimize their cloud setup:- Identify the workload for the cloud: Understand that not all applications are appropriate for the cloud. It's a good idea to assess which applications would gain the most from cloud migration.
- Estimate your resources appropriately: Make a point of selecting only the requisite resources and storage before investing so you don't end up paying for space you don't need.
- Monitor your usage: Regularly monitoring cloud usage can go a long way in ensuring zero cloud wastage. You can also define resource quota policies that prevent unpredicted spikes in usage or limit people who can use and manage cloud resources.
- Regular optimization: Another essential strategy to keep your cloud infrastructure optimized is to adjust workloads periodically and take immediate corrective measures.
- Choose the right managed cloud partner: Selecting a cloud partner with the required expertise, processes, systems, and a track record can help you plan and manage your cloud requirements more effectively.
Synoptek’s Cloud Infrastructure Optimization Services
Synoptek's cloud consulting services equip enterprises at any stage of their cloud journey with a skilled team of professionals. We can assist you with all aspects of your cloud project, including planning, computing, migration, implementation, and management. Our cloud infrastructure optimization services help you identify what components of your cloud are not functioning at their optimum capability. We have highly skilled cloud resources ready to engineer the appropriate fixes to ensure that your cloud infrastructure is paying the greatest dividends it possibly can. Our extensive experience with cloud optimization enables us to make macro and micro level recommendations that will empower you with a better, stronger, faster, comprehensively managed cloud setup with less downtime and greater returns.What are the Benefits of Cloud Migration Services?
Organizations that invest in cloud migration services can experience a wide range of benefits, including:- Cost efficiency: Reduce physical infrastructure costs by shifting to a scalable cloud model.
- Business continuity: Minimize downtime and enhance disaster recovery capabilities.
- Operational agility: Enable faster deployments and adapt quickly to market changes.
- Scalability: Easily scale resources as business needs evolve.
- Enhanced security: Leverage built-in cloud security tools and compliance standards.
How do Cloud Migration Services Enhance Data Security?
Cloud migration services help improve security by implementing strong encryption protocols, identity and access management, real-time monitoring, and automated threat detection. Depending on industry requirements, cloud environments are often equipped with advanced security compliance standards such as ISO, GDPR, and HIPAA. Cloud migration companies also conduct risk assessments and develop mitigation plans tailored to your organization’s security needs.Can Cloud Migration Services Support Hybrid and Multi-cloud Environments?
Yes, professional cloud migration services are designed to support a range of environments, including public, private, hybrid, and multi-cloud architectures. Cloud migration and management services offer configuration and integration solutions that allow organizations to optimize their workloads across multiple cloud platforms without compromising security or performance.What Types of Organizations can Benefit from Cloud Migration Services?
Cloud migration services benefit organizations of all types and sizes, from startups to large enterprises. They are especially valuable for companies aiming to modernize legacy systems, reduce IT overhead, increase system resilience, or enable remote workflows. Cloud migration consulting is particularly useful for regulated sectors like healthcare, finance, and government that require expert planning and adherence to compliance standards.How do I Choose the Right Provider for Cloud Migration Services?
When evaluating cloud migration companies, consider the following factors:- Experience and expertise: Look for providers with a proven track record in delivering cloud migration and management services.
- Comprehensive service offering: Ensure the provider handles end-to-end migration, including planning, execution, and ongoing support.
- Customization: Choose a provider that tailors services to your specific workloads and business goals.
- Compliance knowledge: Ensure they understand and comply with data privacy regulations.
- Post-migration support: Verify that the provider offers ongoing cloud management services for performance optimization and security.
What Challenges do Cloud Migration Services Help Address?
Cloud migration services help organizations overcome critical challenges such as:- Legacy system limitations: Migrate outdated systems to modern platforms without interrupting business operations.
- High infrastructure costs: Shift from CapEx to OpEx model by eliminating the need for on-site hardware.
- Downtime risks: Minimize disruption with carefully orchestrated migration plans.
- Lack of in-house expertise: Leverage external cloud migration consulting to fill skill gaps and reduce errors.
How do Cloud Migration Services Improve Operational Efficiency?
These services improve efficiency by streamlining resource allocation, automating manual tasks, and enabling faster application deployment. Cloud migration and management services allow for centralized control, enhanced performance monitoring, and predictive analytics that drive more intelligent business decisions and operational agility.Can Cloud Migration Services Assist with Compliance Requirements?
Experienced cloud migration companies ensure compliance by aligning your infrastructure with relevant industry regulations such as HIPAA, SOC 2, and GDPR. Through secure data transfer, encrypted storage, and audit-ready documentation, cloud migration ensures compliance gaps are identified and resolved during migration.What is the Role of Cloud Migration Consulting in the Migration Process?
Cloud migration consulting is critical for planning and strategy. It involves assessing the current IT landscape, identifying migration goals, analyzing risks, defining architecture, and creating a roadmap. Consultants guide your organization through the entire cloud migration lifecycle, ensuring maximum ROI while avoiding common pitfalls.
Are you looking to engage with a cloud migration services provider? As experienced cloud migration companies, we offer comprehensive assessment, planning, and implementation services to ensure a smooth transition to the cloud. Contact our cloud migration experts to learn more about how we can support your organization's journey to the cloud.
What is a Digital Customer Experience Strategy?
A digital customer experience strategy is a comprehensive plan that outlines how a company will deliver consistent, meaningful experiences across digital channels. It encompasses websites, mobile apps, social media, and other digital touchpoints to create seamless customer interactions. This strategy aligns digital initiatives with overall business objectives while focusing on customer needs and preferences.How does Customer Experience Strategy Consulting Work?
Customer Experience Strategy consulting uses advanced analytics and customer research techniques to improve business outcomes. Consultants use:- Journey Mapping: Creating detailed visualizations of customer interactions across all touchpoints.
- Voice of Customer (VoC) Programs: Collecting and analyzing customer feedback systematically.
- Experience Design: Developing improved customer interactions based on research findings.
- Implementation Planning: Creating roadmaps for organizational change and technology adoption.
What is a Good Customer Experience Strategy Example?
A leading credit reporting agency partnered with CX consulting experts to enhance its customer experience and shift towards a more customer-centric approach.Challenges Faced
- The agency struggled with customer retention as their products were not meeting customer needs.
- There was no framework for gathering customer insights and improving offerings.
- Customers found it difficult to compare credit reports from different bureaus and understand their credit status.
CX Strategy Implementation
The consulting team designed a structured CX transformation strategy in three key phases:- CX Roadmap Development: Conducted stakeholder interviews and implemented a customer-first framework to improve understanding of customer needs.
- Product Development & UX/UI Enhancements: Designed a new digital tool to help customers compare credit reports easily and understand their financial standing. This included multiple rounds of usability testing to refine the experience based on real user feedback.
- CX Center of Excellence (CoE): Trained product managers to focus on customer needs rather than product features, ensuring long-term customer-centric decision-making.
Business Outcomes
- The new CX strategy helped the agency innovate its product offerings to better align with customer expectations.
- Customers felt more empowered and confident in managing their credit histories.
- The organization witnessed higher engagement and customer satisfaction as users interacted more frequently with its tools and services.
Why is Investing in Customer Experience Consulting Services Important?
Businesses that prioritize CX consulting gain significant competitive advantages, including:- Higher Customer Retention: Satisfied customers are more likely to stay loyal and recommend a brand.
- Increased Revenue: Positive experiences lead to repeat business and higher customer lifetime value.
- Operational Efficiency: Automation and AI-powered solutions reduce costs and improve service delivery.
- Stronger Brand Differentiation: Exceptional CX sets businesses apart from competitors.
- Data-Driven Decision-making: CX consulting helps companies use data insights to refine and improve customer strategies continuously.
What is the Purpose of Cybersecurity Consulting Services?
Cybersecurity consulting services provide organizations with expert and experienced guidance on enhancing their security posture. A cybersecurity consultant evaluates existing security measures, identifies vulnerabilities, and recommends necessary risk mitigation and compliance strategies.What are Managed Cybersecurity Services?
Managed cybersecurity services offer organizations comprehensive security solutions, including threat monitoring, incident response, and compliance management. These services enable businesses to leverage expert resources and technology to enhance their security without investing in hiring, training, and maintaining an expensive in-house talent pool.How can Cybersecurity Managed Services Benefit my Organization?
Cybersecurity managed services can enhance your organization’s security posture by providing continuous monitoring, rapid incident response, and access to the latest security technologies. This lets you focus on your core operations while allowing skilled professionals to take care of your cybersecurity needs.What Should I Look for in a Cybersecurity Consulting Services Provider?
When looking for a cybersecurity consulting services provider, consider the following key factors to ensure you choose the right expert for your organization's needs:- Experience and Expertise: Look for relevant certifications and industry experience in areas such as cybersecurity risk analysis, vulnerability assessment, and security testing services.
- Types of Services Offered: Ensure cybersecurity consulting services provider delivers a comprehensive suite of cybersecurity services, including cybersecurity consulting services, managed cybersecurity services, and application security consulting.
- Customized Solutions: Partner with a provider who will assess your specific security needs and develop tailored strategies. Look for someone who conducts thorough cybersecurity assessments and can conduct detailed cybersecurity risk analysis.
- Incident Response Planning: Ensure the partner has a clear plan for managing security breaches and provides ongoing support so your organization can respond swiftly to incidents.
What is Cybersecurity?
Cybersecurity is a collection of methodologies, technologies, and processes used to safeguard an organization’s computer systems, networks, and data from cyberattacks or unauthorized access. The primary motive of cybersecurity is to shield all corporate assets from external and internal threats, as well as from natural disasters.
How Does Cybersecurity Work?
Cybersecurity systems detect, examine, and fix potential system weaknesses and vulnerabilities before hackers or malicious software exploit them. An organization, its employees, and the processes and technologies must come together to create a solid cybersecurity layer that protects it from potential attacks.
Why Is Cybersecurity Important?
In today's tech-driven world, the increasing accessibility of sensitive information online emphasizes the need for robust cybersecurity measures. Frequent high-profile breaches highlight the financial and reputational damage cyberattacks can inflict. As cyber threats continue to surge, businesses of all sizes are extremely vulnerable to attacks.
What Are the Different Types of Cybersecurity?
In the world of cybersecurity, there are several key areas that help keep IT infrastructure safe. These include application, cloud, data, mobile, and network security. Let's take a brief look at each to understand their roles in keeping businesses protected online.
1. Application Security
Application security refers to the practices, procedures, and strategies used to protect web and mobile applications against security threats and vulnerabilities. These threats can include malicious activities such as unauthorized access, data breaches, injection attacks (such as SQL injection), denial of service (DoS) attacks, and more.
2. Cloud Security
Cloud security refers to a set of policies, technologies, practices, and controls designed to protect data, applications, and infrastructure stored and processed in cloud computing environments. This specialized field of cybersecurity focuses on protecting cloud-based assets from multiple threats, including unauthorized access, data breaches, data loss, and service disruptions.
3. Data Security
Data security involves safeguarding digital information throughout its entire lifecycle to prevent corruption, theft, or unauthorized access. This comprehensive approach encompasses hardware, software, storage devices, user devices, access controls, administrative measures, and organizational policies and protocols.
4. Mobile Security
Mobile security refers to a set of practices, initiatives, and technologies designed to protect mobile devices (such as smartphones, tablets, and laptops) and the information stored or transmitted on them from various security threats, including spam, phishing, ransomware, theft, misuse, etc.
5. Network Security
Network security refers to the practices, measures, and technologies put in place to protect computer networks and the data transmitted over them from various security threats and unauthorized access. Network security involves implementing safeguards such as firewalls, intrusion detection systems, encryption, access controls, and regular monitoring to detect and mitigate cyber threats.
Are Cybersecurity and Information Security the Same?
No, cybersecurity and information security are not the same thing, although they are closely related. Information security primarily focuses on safeguarding data from unauthorized access or manipulation. Cybersecurity, on the other hand, is a broader field that encompasses all aspects of security, including protecting devices, networks, and systems from cyber threats. This goes beyond data and includes protecting entire digital ecosystems. While they have distinct focuses, both information security and cybersecurity work together to ensure that an organization and its data are secure and that its digital infrastructure is resilient to cyber-attacks.
Why Does an Organization Need Cybersecurity?
Attackers are constantly threatening the digital assets of your company. Therefore, there is a continuous need to protect them. Here are the top reasons why IT security is vital to your business:
- Cyber-attacks aren’t going away any time soon: Thanks to technological advancements, the world is becoming more connected. Cybercriminals are also developing more advanced attack strategies. It’s vital to keep up with what’s going on in the cybersecurity domain to protect the data environment. Since most modern businesses depend highly on technology, they need to incorporate cybersecurity into their corporate DNA.
- It assists you in cost-cutting: Putting a cybersecurity policy in place might seem like a costly endeavor. However, because cyber intrusions have far-reaching cost repercussions in terms of poor business reputation, legal fees, and lost customer trust, in actuality, businesses save money in the long run with a robust security policy in place.
- Cybersecurity provides investors and clients with an assurance of safety: Typically, venture capitalists prefer to invest in cyber-secure organizations. Since an organization must guarantee data integrity, availability, and confidentiality to attract customers and investors, investing in cybersecurity is a great way to provide them with an assurance of safety and security.
- Compliance with regulations: Businesses must meet several regulatory standards relating to information security to become compliant with industry and government regulations. These include HIPAA, SOX, PCI DSS, and GDPR. Failure to follow the rules might result in significant fines and penalties.
What are the Different Types of Cybersecurity Attacks?
As businesses get increasingly digital, cybercrime has only found new ways to deepen its grip.
Listed below are the most significant types of cybersecurity attacks in the current times:
- Ransomware attacks: Ransomware attacks involve gaining access to a user’s data and prohibiting them from using it until a ransom is paid. Ransomware attacks are dangerous for individual users, but they’re much more dangerous for organizations because they prohibit organizations from accessing vital data they need to run their day-to-day operations.
- Phishing attacks: Phishing is a social engineering attack frequently used to gain sensitive data from users, such as login credentials. Hackers take advantage of it for their gains, such as internet shopping and money laundering.
- Attacks on Blockchain and Cryptocurrency: Attacks on blockchain and cryptocurrency pose considerable challenges in cybersecurity for businesses as they can compromise customer data and business operations. Organizations must be aware of the security risks associated with these technologies and ensure that no security gaps exist for intruders to exploit.
- Distributed Denial-of-Service (DDoS) attacks: A Distributed Denial-of-Service (DDoS) assault includes flooding the server with large amounts of traffic to knock down a business website. In recent years, such attacks have become frequent.
- Remote and Cloud attacks: The new wave of digitization and widespread success of hybrid working have led to an increased adoption of cloud-based technologies. However, some of the digital advancements were so quick that the security aspect was not given enough consideration, making cybersecurity breaches easy.
- IoT vulnerability: A wide range of businesses has adopted IoT app development to analyze customer and client behavior and develop efficient marketing procedures. As IoT grows in popularity without equivalent technological advancements to protect against cybercrime, the threat level is only getting worse.
Considering Synoptek for Your Cybersecurity Needs
Synoptek’s Cybersecurity Services will increase your IT team’s ability to safeguard applications, computing, and network infrastructure with modern security solutions that are fully managed, simple to adopt, and do not require substantial upfront investments. Synoptek’s Managed Cybersecurity Services are updated regularly, allowing businesses to cope with new threats in a competent and timely manner.
Our cybersecurity experts have the capacity to reverse-engineer malware and other suspect applications to extract vital information that can be utilized to create new security content that will safeguard the entire client base from future breaches. When it comes to cybersecurity, Synoptek has the following offerings:
- Security Program Diagnostics
- Unified Endpoint Security
- Cybersecurity Threat Hunting and Management
- Ransomware Defense and Protection Services
- Cybersecurity Risk Management Framework
- Managed Cybersecurity Services
To know more about Synoptek’s Cybersecurity framework, please click here.
Reasons to Consider Predictive Analytics
Standard business information and reporting provide insights that are not immediately actionable; businesses must turn them into action with their analysis and judgment. On the other hand, predictive analytics is developed exclusively to provide decisive action imperatives. It helps organizations make well-informed business decisions without involving human judgment. Organizations can use predictive analytics to:- Develop a competitive edge by leveraging meaningful business insights
- Understand customer journey and behavior and leverage this understanding to increase sales and provide excellent customer experience
- Recommend new products to customers based on their purchasing behavior or search patterns
- Analyze customers’ purchase capacity, needs, and other behavior, and evaluate opportunities for up-sell and cross-sell
- Deliver quick gratification to customers through personalized suggestions and recommendations
- Prevent fraud by anticipating possibilities of a security breach
- Read industry versus organization trends and make necessary adjustments to remain profitable
- Determine the likelihood of customer churn
The Added Benefits of Predictive Analytics
Apart from helping businesses predict outcomes, and therefore, making informed business decisions, predictive analytics also helps organizations improve their business operations and refine their marketing campaigns.- Many companies use predictive models to forecast inventory and manage resources. For example, airlines use it to determine ticket prices, restaurants use it to predict daily footfalls and increase profit margins.
- Several businesses use predictive analytics to fine-tune their marketing campaigns. They recognize the most successful combination of product bundles, content, medium, and timing to target a specific consumer. These techniques help them attract, retain, and engage their most valuable customers.
How Synoptek Can Support Your Predictive Analytics
Synoptek has a highly skilled team with a broad spectrum of functional and technical knowledge related to predictive analytics. Predictive analytics is an offering under our Artificial Intelligence service. As businesses seek to nurture more relevant and meaningful connections with consumers, our predictive analytics service, tailored to their individual needs, allows them to create and sustain long-lasting customer relationships. Other related service offerings provided by Synoptek are: To know more about Predictive Analytics, click here.Artificial Intelligence (AI) is a system that can demonstrate human intelligence capabilities like reasoning and learning. This ability to simulate human comprehension aids problem-solving and decision-making.
Generative AI (GenAI) is a subset of artificial intelligence. It leverages large language models (LLMs) to create new content, including texts, images, audio, and videos. Trained on vast amounts of data, it can generate outputs that resemble human-created content without directly copying the original data.
Humans can use generative AI tools for chatbots, image synthesis, music composition, and code generation applications.
What is the Difference Between Generative AI and Predictive AI?
Generative AI tools use existing information to create new data according to human prompts. For example, developers can provide a generative AI system with a prompt that enables the system to offer code suggestions.
Predictive AI systems use past or present data to forecast what could happen in the future. For example, financial institutions can use predictive AI models to predict market trends and stock prices based on emerging economic factors.
How does GenAI Work?
Generative AI relies on advanced machine learning techniques, such as deep learning and neural networks, to analyze data patterns and generate relevant outputs.
It uses architectures like transformers (e.g., GPT models), diffusion models (for image generation), GANs (Generative Adversarial Networks), and VAEs (Variational Autoencoders) to produce high-quality content.
The model generates responses based on user prompts, continually refining its outputs through iterative learning and fine-tuning.
What are Some Examples of Generative AI?
Examples of generative AI are many, with use cases such as:
- Intelligent Bots: companies can build customized chatbots for any application, enabling users to query and receive quick responses.
- Content Generation: Generative AI can automate content generation for various marketing and social media platforms, enabling the creation of engaging and personalized blogs, campaigns, posts, captions, and visuals.
- Image Generation: Generative AI can learn from large sets of images and generate new unique images based on trained data.
- Video Synthesis: GenAI models can create new video content by generating future frames from a sequence of input frames.
- Code Generation: Generative AI systems can speed software development by creating, reviewing, and translating code from one language to another.
What are the Advantages of Generative AI?
The advantages of generative AI tools are many for businesses across industries, such as:
- Automating repetitive tasks
- Enhancing creativity and innovation
- Improving customer experiences with personalized interactions
- Reducing time-to-market for products
- Supporting data augmentation and simulations like generating draft responses
What are the Challenges of Generative AI?
Generative AI tools offer many benefits, but organizations must also know about generative AI implementation risks. These include:
- Transparency: Organizations or users might not always understand how GenAI models work.
- Accuracy: Generative AI systems may produce inaccurate and biased answers, impacting critical business decision-making.
- Security and compliance: GenAI depends on large amounts of data. This creates a data breach or misuse risk, which can affect compliance.
- Intellectual property (IP): Lack of proper data governance and protection assurances can put confidential enterprise information at risk.
- Ethical Use: As GenAI advances, there is a growing risk of misuse, such as deepfakes.
- Skills Gap: Many organizations eager to adopt GenAI struggle with successful implementation due to the lack of necessary GenAI skillset.
The field of decision intelligence blends business intelligence (BI) and artificial intelligence (AI) to improve organizations' decision-making processes. With Decision Intelligence, business decisions can be made more quickly, accurately, and consistently, leveraging a host of advanced predictive models.
The purpose of Decision Intelligence is to assist businesses in identifying opportunities, developing strategies, making plans, launching projects, and predicting results. Decision Intelligence models enable companies to maximize their efforts by providing valuable insights into business operations.
What Are the Added Benefits of Decision Intelligence Platforms?
Platforms offering Decision Intelligence facilitate decision-making and provide insights, recommendations, and context, enabling organizations to realize better value from technology investments. A few of the key benefits include the following:
- Decisions can be based on concrete data
- Actions can be taken in real-time. Companies can gain a competitive advantage
- Meeting customer needs becomes easier
- Organizations can move beyond dashboards to understand analytics
- Insight discovery and automation can be enhanced
- They can determine hazards based on past and current data and propose management solutions
- Delivering actionable recommendations and accommodating human judgments like intuition also becomes possible
How Do You Get Started with Decision Intelligence?
Decision Intelligence is considered the biggest B2B movement of this generation. Decision Intelligence is AI with a purpose that leads to growth, efficiency, profit, and sustainability. To get started with Decision Intelligence, you need:
- An established data infrastructure
- A team of experienced SMEs
- AI and machine learning investments
- Clarity on use cases
- Value-driven business culture rather than a self-service culture
Using Decision Intelligence, users can identify patterns, and connections, to find the best solution to all unforeseen circumstances.
How Can Synoptek Help Your Organization Make Intelligent Decisions?
Synoptek understands that each organization has specific needs when it comes to data. Therefore, we tailor our insights services to help our clients meet their goals.
Whether you are at the very start of your data insights journey or are trying to transition to the next stage, Synoptek can help you translate your goals into an actionable roadmap.
In the realm of data insights, Synoptek offers the following services:
- Business Intelligence and Analytics Consulting
- Data Warehouse Services
- Big Data Engineering
- Data Science and Artificial Intelligence
- Analytics as a Service (AaaS)
- Data Visualization and Analytics
To learn more about Synoptek’s Data Insights offering, please click here. To speak with a Decision Intelligence consultant, contact us today.
What is Big Data Analytics?
Big data is the vast and complicated data that typical data processing systems can't collect, manage, or handle. Big data could be structured, unstructured, or semi-structured. The practice of evaluating, cleansing, transforming, and modeling this data to uncover usable information and meaningful conclusions is known as big data analytics.Why Big Data Analytics Consulting?
Big data analytics helps businesses make the most of their enterprise data by- Finding new business opportunities
- Accelerating the decision-making process
- Alerting the enterprise by identifying underlying danger and problems
The Benefits of Big Data Analytics Consulting
Big data consulting services help organizations leverage advanced data analytics to process datasets, derive business insights from them, and also suggest the most effective strategy to leverage this data. By partnering with big data consulting firms, organizations can:- Get customized recommendations based on the organization's current enterprise setup and expected outcomes
- Roll out the big data initiatives faster
- Focus on their core job instead of worrying about the big data solution implementation
- Adhere to compliance and regulatory guidelines without worrying about jeopardizing the big data projects
- Apply industry best practices to get faster and better results
Why Synoptek's Big Data Analytics Consulting
Synoptek can help you determine the big data technologies that are suited for your business, how to integrate them, and how to manage them as part of your Business Intelligence (BI) and advanced analytics setup. We can aggregate and integrate your data to have all the tools you need to gain relevant insights and make the best decisions possible. Synoptek endeavors to provide a big data service that is fast, unique, and efficient, and our current offering includes the following services:- Big Data Collection
- Big Data Processing
- Big Data Analysis
- Big Data Innovation
- Big Data Planning
How is a B2B E-commerce Solution Different from a B2C E-commerce Solution?
While both models focus on online transactions, there are key differences between B2B and B2C e-commerce solutions:- Order Size and Volume: B2B transactions involve bulk orders, while B2C focuses on individual purchases.
- Pricing and Negotiations: B2B platforms support custom pricing, bulk discounts, and contract-based pricing, unlike fixed pricing in B2C.
- Payment and Invoicing: B2B E-commerce allows for credit terms, multi-stage approvals, and invoicing, whereas B2C typically supports instant payments.
- Customer Relationships: B2B models emphasize long-term relationships and account-based purchasing, while B2C is transaction-focused.
How Can a B2B E-commerce Solution Benefit Businesses?
B2B e-commerce solutions offer several advantages, including:- Operational Efficiency – Automates manual processes, reducing order errors and processing times.
- Scalability – Supports business growth by handling large product catalogs and high-volume transactions.
- Personalized Customer Experience – Enables account-based pricing, contract negotiations, and customized purchase workflows.
- Seamless Integrations – Connects with ERP, CRM, and supply chain management systems for smooth operations.
- Data-Driven Decision Making – Provides insights on sales, customer behavior, and inventory to optimize business strategies.
How to Choose the Right B2B E-commerce Solution Provider?
Selecting the right B2B E-commerce solution provider is crucial for business success. Consider the following factors:- Business Model and Scalability – Ensure the provider supports your business type (B2B, B2C, or hybrid) and can scale as your business grows.
- Customization and Flexibility – Look for a solution that allows custom workflows, pricing models, and integrations to meet your unique business needs.
- Integration Capabilities – The platform should integrate seamlessly with ERP, CRM, and inventory management systems to avoid operational silos.
- Security and Compliance – Check for industry-standard data security measures, including PCI-DSS compliance, encryption, and fraud prevention tools.
- User Experience and Mobile Optimization – A responsive design and intuitive interface improve engagement and conversions across all devices.
- Support and Maintenance – Reliable technical support, updates, and training ensure smooth long-term operations.
- Pricing and Total Cost of Ownership – Compare subscription fees, transaction costs, and additional expenses to determine overall affordability.
What Services are Typically Included in Helpdesk Outsourcing?
Helpdesk outsourcing providers offer a wide range of services designed to comprehensively support an organization's IT needs. These services can be tailored to meet the specific requirements of different organizations, ensuring that all essential support functions are covered.- First-level user support for hardware and software issues
- Remote troubleshooting and problem resolution
- Ticket management and escalation
- Password resets and account management
- Basic network support
- Application support
- Asset and inventory management
- Reporting and analytics on support activities
How Does Helpdesk Outsourcing Impact an Organization's Internal IT Team?
When a company decides to outsource its helpdesk, it inevitably causes shifts in the internal IT team's roles and responsibilities. This transition can lead to opportunities and minor changes for in-house IT professionals.- Frees up internal IT staff to focus on more strategic projects
- Reduces the burden of routine support tasks on specialized IT personnel
- May require adjustments in roles and responsibilities of in-house IT staff
- Can lead to knowledge transfer and best practice sharing between the outsourced team and internal IT
How can Companies Ensure Successful Helpdesk Outsourcing?
Successfully outsourcing a 24/7 IT helpdesk requires careful planning, clear communication, and ongoing management. By following best practices, companies can create a strong foundation for a productive and beneficial outsourcing relationship.- Clearly define scope, expectations, and SLAs in the outsourcing contract
- Choose a provider experienced in offering managed helpdesk services and familiar with your industry
- Establish strong communication channels between internal teams and the outsourced helpdesk
- Implement robust security measures and compliance protocols
- Regularly review performance metrics and user satisfaction
- Maintain some level of in-house IT expertise for oversight and strategic direction
What are the Different Models of Managed Helpdesk Services?
Managed helpdesk services are not a one-size-fits-all solution. Various models are available, each with its own advantages and considerations. Understanding these models can help organizations choose the approach that best suits their needs.- Fully outsourced: The entire helpdesk function is handled by the third-party provider
- Co-managed: The organization retains some control and works alongside the outsourced team
- Selective outsourcing: Only specific aspects of helpdesk support are outsourced
- Onshore, offshore, or nearshore: Outsourcing to providers in the same country, overseas, or in nearby countries, respectively
- 24/7 IT helpdesk: Around-the-clock support provided by the outsourcing partner
Help Desk and Technical Support refers to the services provided by IT professionals to assist users with IT-related problems, software issues, and other technical difficulties. This support can range from basic troubleshooting to complex problem-solving and is typically organized into different tiers based on the level of expertise required.
Is There a Difference Between Help Desk and Technical Support?
While the terms are often used interchangeably, there are some distinctions:
- Help Desk: Refers to the first point of contact for users seeking IT assistance. Help desk staff typically handle basic issues and user queries and route more complex problems to appropriate specialists.
- Technical Support: Involves more in-depth, specialized assistance for complex technical issues. Technical support staff usually have more advanced knowledge and skills in specific areas of IT.
In practice, many organizations integrate both functions, with the 24/7 IT help desk serving as the initial point of contact before escalating to more specialized technical support team when necessary.
What Types of Issues do Help Desk and Technical Support Teams Handle?
Helpdesk support services teams are equipped to handle a wide range of technical and IT-related issues that users may encounter in their daily work. Some common areas of support include:
- Hardware troubleshooting (e.g., computer, printer, network device issues)
- Software installation and configuration
- Account management and access issues
- Network connectivity problems
- Email and communication tool support
- Operating system support
- Data backup and recovery assistance
- Malware and security incident response
A 24/7 IT help desk ensures that these issues can be addressed anytime, providing users with continuous access to support.
How Does 24/7 IT Help Desk and Technical Support Benefit an Organization?
Implementing a robust 24/7 IT Help Desk and Technical Support system offers numerous advantages to an organization. Key benefits include:
- Improved productivity by quickly resolving IT issues
- Enhanced user satisfaction through prompt and effective support
- Reduced downtime of critical systems and applications
- Better resource allocation by tracking and analyzing support trends
- Increased IT efficiency through standardized processes and knowledge sharing
- Improved security posture by addressing technical vulnerabilities promptly
- Cost savings by preventing small issues from escalating into major problems
With helpdesk support services, organizations can further reduce downtime and ensure uninterrupted support.
Are you looking for professional IT Helpdesk Services in Orange County? Our team of experienced IT professionals offers comprehensive support solutions tailored to your specific needs. Contact us to learn how we can help improve your user support experience and boost overall IT efficiency.
IT infrastructure assessment comprehensively evaluates an organization’s existing IT infrastructure, including servers, networks, storage systems, software, and security protocols. The goal is to identify current capabilities, uncover vulnerabilities, ensure alignment with business goals, and create a roadmap for transformation.
What are the Key Benefits of an Infrastructure Assessment?
Conducting a comprehensive IT infrastructure optimization can deliver a variety of strategic and operational advantages:
- Enhanced Performance: Identify bottlenecks and improve system efficiency.
- Risk Mitigation: Detect vulnerabilities and address security gaps.
- Cost Savings: Optimize resource usage and reduce unnecessary expenses.
- Future Readiness: Ensure infrastructure can support future growth and emerging technologies.
- Strategic Alignment: Align IT infrastructure with overall business goals through IT infrastructure optimization.
When Should an Organization Conduct an Infrastructure Assessment?
Organizations should consider an IT infrastructure assessment during the following:
- Business expansion or digital transformation initiatives
- Migration to new platforms, such as cloud environments
- Recurring performance issues or outages
- Compliance preparation for industry regulations
- Mergers, acquisitions, or organizational restructuring
How Does an Infrastructure Assessment Improve IT Security?
An IT infrastructure assessment is critical in strengthening IT security by identifying unmanaged assets, outdated software, misconfigured systems, and potential entry points for cyber-attacks.
The assessment often results in recommendations that include enhanced firewalls, updated antivirus solutions, role-based access controls, and other security best practices aligned with compliance standards identified through a comprehensive IT infrastructure audit.
Can Infrastructure Assessments Support Cloud Readiness?
IT infrastructure optimization is a critical first step in determining cloud readiness. It evaluates existing workloads, hardware compatibility, network capacity, and data sensitivity, helping organizations plan successful cloud migrations. IT infrastructure consulting teams often use the assessment phase to develop customized cloud strategies based on organizational needs.
What Types of Organizations Benefit from Infrastructure Assessment Services?
IT infrastructure assessment services can benefit organizations across all sectors—healthcare, finance, education, manufacturing, and professional services. These evaluations are beneficial for mid-size to large enterprises with complex systems or growing compliance obligations. IT infrastructure consulting firms often tailor assessments to specific industry standards and business models.
What Should You Expect From an Infrastructure Assessment?
A comprehensive IT infrastructure assessment typically includes:
- Inventory and mapping of all hardware and software assets
- Performance analysis of servers, storage, and networks
- Security posture evaluation and vulnerability detection
- Recommendations for upgrades, IT infrastructure optimization, and risk mitigation
- A detailed report and strategic IT roadmap
How do Infrastructure Assessment Services Support Compliance Requirements?
Many regulatory standards require secure, reliable tech environments. An IT infrastructure optimization activity helps identify areas where systems may fall short—such as data encryption, user access controls, backup practices, or software patch management. When conducted by specialized IT infrastructure consulting providers, these assessments help ensure compliance with HIPAA, PCI-DSS, and SOC 2 standards through comprehensive IT infrastructure audits.
What are Common Challenges Resolved by Infrastructure Assessments?
IT infrastructure assessments help address these common challenges:
- Outdated or unsupported technology
- Redundant systems and underutilized assets
- Cybersecurity vulnerabilities or data breaches
- Poor network performance or downtime issues
- Lack of IT scalability to support growth
What is the Role of Infrastructure Consulting in the Assessment Process?
IT infrastructure consulting firms bring expertise and industry best practices to the assessment process. They conduct in-depth evaluations, interpret complex IT data, and develop actionable strategies. As experienced technology partners, consultants ensure recommendations align with current infrastructure realities and long-term business goals—including improved risk management and IT infrastructure optimization.
Are you thinking about optimizing your technology environment? Start with a comprehensive Infrastructure Assessment. Our expert infrastructure consulting team provides end-to-end evaluation services to help you maximize performance, reduce risk, and plan. Contact us today to discuss your IT infrastructure needs.
- Determine the threats to your essential systems and sensitive information.
- Identify and categorize your data according to the severity of the danger involved.
- Take steps to mitigate the risks.
Benefits of a Data Protection Risk Assessment
Organizations are vulnerable to various sophisticated data breaches because they collect, store, and use a massive amount of personal data to make better business decisions. From personal data being stolen and released to it being misused by criminals, the demand to comply with evolving legislation like the GDPR is rising. Data protection evaluations are an excellent approach to secure data privacy while also making informed judgments about reducing or eliminating risks. It also helps protect the privacy and confidentiality of personal data while increasing client trust. A robust first line of defense makes sure that most risks are managed before they become threats. It also ensures that the company is prepared to recover as quickly and safely as feasible in the event of an adverse incident. When employees don’t have to worry about the risks individually, they are fully engaged with their core tasks, and the organization's overall productivity increases.Data Protection Risk Assessment Challenges
Data Protection Risk Assessment Challenges are as follows:- Budget Restriction: Organizations' strict budgetary allocations may make it difficult to choose a superior approach that requires more resources and time over a sub-par process that requires fewer resources and time.
- Unstructured and Non-Formal Approach: The absence of a formal methodology and structured approach might lead to a risk assessment that is insufficient to protect the asset.
- Improving Risk Assessment and Modeling: This is a difficult task because the stages involved in Risk Assessment must be carefully modified according to their feasibility, and care must be taken to ensure that:
- The final steps identified are the required steps
- Critical steps have not been missed
- The steps are ordered in the correct sequence
- Developing Risk Metrics: An incorrectly prioritized threat or vulnerability will result in either over-controlling or under-controlling. Over-controlling will add to the system's cost burden, while under-controlling will make it more vulnerable to attack.
- Data Management and Reporting: The capacity to evaluate data collected during an evaluation is influenced by the consistency and organization of that data. As a result, methods and templates must be used to control the volume and quality of assessment data.
Where Synoptek Can Support Your Strategy?
Synoptek assists your company with disaster preparedness by conducting thorough IT risk and data security assessments, allowing you to discover gaps, develop appropriate processes, and manage risks that could result in downtime. Synoptek can help you protect your data and develop and implement business continuity plans to help you prepare for a disaster. The Data Protection and Availability Assessment Services provided by Synoptek include the following:- Perform a baseline evaluation: Synoptek assesses the present state of your enterprise data protection and availability strategy and creates practical suggestions and roadmaps wherever needed.
- Identify Vital Apps/Operations List: Synoptek collaborates with key stakeholders to identify and prioritize each of your organization's critical applications, processes, and people.
- Establish Maximum Tolerable Outage Allowances: Synoptek can assist in determining the maximum time each system can be out of service after an occurrence.
- Execute a Business Impact Study: As part of Synoptek's IT risk management services, senior consultants collaborate with business leaders to conduct a business impact analysis to document the financial impact of a service disruption on your organization's mission.
- Conduct Strategic Leadership Workshops: Synoptek offers online and on-site training programs and workshops to guide stakeholders through the critical steps of building and managing an effective IT risk management and data security assessment plan.
24/7 helpdesk monitoring and support is an around-the-clock support model that helps businesses or individual users with technical assistance for monitoring IT systems or resolving user issues. A 24/7 IT helpdesk ensures that users can access support anytime, regardless of the hour or day, including nights, weekends, and holidays.
How is 24/7 Helpdesk Monitoring and Support Offered?
A 24/7 IT helpdesk allows users to get help and find answers to IT-related queries almost immediately. Companies offering 24/7 helpdesk support services often do this via:
- Phone or email support that allows users to describe their issues in detail
- Live chat via dedicated support portals
- A self-service knowledge base for quick answers to common questions
- Ticketing systems where users can log in their issues
- AI-enabled chatbots that provide decent first-level helpdesk support
What are the Benefits of 24/7 IT Support Services?
24/7 helpdesk support services ensure users get access to support anytime, including nights, weekends, and holidays. An IT helpdesk support company offering 24/7 IT support services helps:
- Minimize system downtime via continuous monitoring, ensuring issues are detected and resolved before they cause performance or availability issues.
- Enhances security by identifying security loopholes in time and preventing incidents of cybersecurity attacks or data breaches.
- Boost workforce productivity and efficiency by ensuring users receive prompt and accurate assistance with IT problems that affect their day-to-day tasks.
What Should I Look for in an IT Helpdesk Support Company?
While looking for an IT helpdesk support company, there are several aspects to look for:
- Presence of a global delivery model to ensure support across locations and time zones.
- Range of services offered, such as software support, hardware troubleshooting, network monitoring, security management, end-user support, etc.
- Robust SLAs with clearly defined response and resolution times, uptime guarantees, etc.
- A large pool of qualified and certified technicians who can handle complex issues and carry out advanced troubleshooting.
Are you looking for professional IT helpdesk services in Orange County? As an award-winning, top-ranked technology consulting and managed service provider (MSP) in Orange County, we offer a range of 24/7 IT Support and Maintenance Services. Contact our helpdesk support services experts in Orange County to know more.
Why are IT Infrastructure Services Important?
IT Infrastructure Services are crucial for organizations as they form the backbone of operations across all industries, ensuring seamless functionality, data security, and competitive advantage. With an increasing reliance on technology, these services help optimize IT environments, reduce downtime, and enhance overall efficiency. Additionally, IT infrastructure consulting provides expert guidance to meet specific business needs.Why do Organizations need IT Infrastructure Support Services?
Organizations of all sizes and any industry require IT Infrastructure Services to:- Support Business Operations: Provides the necessary technology backbone for daily operations and customer interactions.
- Enhance Efficiency: Streamlines processes, reduces downtime, and improves overall productivity.
- Facilitate Scalability: Allows ease in scaling resources to meet increasing or decreasing demands.
- Ensure Security: Protects sensitive data and complies with regulatory requirements through secure configurations and monitoring. Leveraging IT Infrastructure managed services can further enhance these benefits by providing proactive monitoring and maintenance.
What are the Common Pitfalls to Avoid for Infrastructure Optimization?
When optimizing IT infrastructure, organizations should be aware of several common pitfalls:- Over-Optimization: Focusing solely on cost savings can lead to performance issues; balance is key.
- Lack of Monitoring: Failing to monitor infrastructure regularly can result in undetected anomalies and performance degradation.
- Ignoring Security Features: Not understanding or implementing security measures can expose systems to vulnerabilities.
- Inadequate Training: Insufficient training for staff on new technologies can minimize effective management and utilization of resources.
- Poor Resource Allocation: Mismanagement of resources can lead to unnecessary costs; efficient allocation is crucial. IT infrastructure consulting services can help identify and address these issues effectively.
What are the Top IT Infrastructure Management Best Practices?
To modernize technology systems and scale infrastructure effectively, organizations should consider the following best practices:- Adopt Cloud Solutions: Transitioning to cloud-based services can enhance scalability and flexibility while reducing on-premises hardware costs.
- Implement Automation: Utilizing automation tools can streamline operations, improve efficiency, and reduce human infrastructure management errors.
- Regular Audits and Reviews: Frequent assessments of the infrastructure ensure that it meets current business needs and incorporates the latest technologies.
- Partner with IT Infrastructure Managed Service Providers (MSPs): Leveraging MSPs can provide expertise in managing complex infrastructures while allowing internal teams to focus on core business activities.
- Develop a Clear Strategy: A comprehensive modernization plan with scalability, security, and performance goals will help in seamless and successful implementation.
What are Infrastructure Management Services?
Infrastructure management services, or IT infrastructure services, are comprehensive activities to manage, maintain, and optimize an organization's IT infrastructure. These services encompass various tasks related to hardware, software, networks, and data centers, ensuring that all components work together efficiently to meet business needs. Infrastructure management services include network management, server management, data storage solutions, cloud services, security management, and ongoing monitoring and support.How do Infrastructure Management Services Benefit my Organization?
Infrastructure management services provide several benefits, including improved system reliability, enhanced performance, and cost savings through optimized resource use. They offer the ability to focus on core business activities while IT experts manage the complexities of day-to-day infrastructure management.How can Infrastructure Optimization Improve my IT Operations?
Infrastructure optimization involves analyzing and enhancing the efficiency of IT resources. By optimizing your infrastructure, a qualified IT infrastructure services provider can reduce costs, improve performance, and ensure that your IT systems can scale to meet future demands, ultimately leading to better overall business performance.Can Infrastructure Managed Services Help with Compliance and Security?
Yes, infrastructure managed services can significantly enhance compliance and security. Managed service providers typically implement best practices and industry standards to ensure that your IT infrastructure meets regulatory requirements and is protected against various security threats.What Should I Consider When Choosing an Infrastructure Management Services Provider?
When selecting a provider for infrastructure management services, consider their experience, areas of expertise, service offerings, customer support, security measures, and ability to customize services to meet your specific needs. Additionally, look for IT infrastructure services providers with a proven track record in infrastructure optimization.How can I get Started with Infrastructure Management Services?
Are you looking for professional IT infrastructure management services in Orange County? As an award-winning, globally trusted technology consulting and managed service provider (MSP) in Orange County, we offer a comprehensive range of 24/7 IT infrastructure management services. Contact our infrastructure management service experts to learn more.What is IT Help Desk Support?
IT Help Desk support is a 24/7 service that provides technical assistance to users experiencing issues with their systems, software, or other IT-related problems. It serves as the first point of contact for employees or customers seeking help with technology-related issues.What is the Role of IT Help Desk Support?
The role of IT help desk support is to provide prompt and efficient solutions to technical problems, ensuring minimal disruption to business operations. This includes troubleshooting hardware and software issues, assisting with password resets, and escalating complex problems to specialized IT support teams when necessary.What is the Difference Between IT Help Desk Support and IT Support Services?
While both are related, IT help desk support typically focuses on immediate, front-line assistance for common issues, often available 24/7. IT support services, on the other hand, encompass a broader range of technical support, including network management, system administration, and long-term IT strategy planning.Why is 24/7 IT Helpdesk Support Important for Businesses?
24/7 IT helpdesk support is essential for businesses because technology issues can arise anytime, potentially causing significant disruptions. Having around-the-clock support ensures that problems can be addressed promptly, minimizing downtime and maintaining productivity, regardless of when issues occur.What Types of Issues Can IT Helpdesk Services in Orange County Typically Handle?
IT Helpdesk Services in Orange County can handle a wide range of issues, including:- Software installation and troubleshooting
- Hardware diagnostics and repair
- Network connectivity problems
- Email and communication tool support
- Data backup and recovery assistance
- Security-related concerns
- Operating system updates and patches
How Can Outsourcing Helpdesk Support Services Benefit a Company?
Outsourcing helpdesk support services can provide several benefits:- Access to 24/7 IT support without the need to maintain an in-house team around the clock
- Cost savings on training and infrastructure
- Scalability to handle fluctuating support demands
- Access to a wider pool of expertise and specialized knowledge
- Allowing in-house IT staff to focus on strategic projects rather than day-to-day support tasks
- Extensive industry experience and technical expertise
- A wide range of managed IT services
- Robust security measures and compliance adherence
- Excellent customer support and communication
- Proven track record of successful implementations
- Ability to adapt to emerging technologies
What Questions Should You Ask Potential IT Service Partners?
When evaluating potential IT service partners, consider asking:- What is your experience in our industry?
- How do you ensure data security and maintain compliance with industry regulations?
- What is your approach to disaster recovery and business continuity?
- How do you stay updated with emerging technologies, and how can you help us leverage them?
- Can you provide references from clients with similar needs as ours?
- What is your pricing model, and are there any hidden costs?
- How do you measure and report on service quality and performance?
- What is your process for scaling services as our business grows?
Why is Choosing the Right IT Service Provider Crucial?
Selecting the right IT service provider is critical for your organization's success because it can:- Enhance operational efficiency by streamlining your IT infrastructure and processes.
- Reduce risks through proactive monitoring and management of your IT environment.
- Drive innovation by leveraging cutting-edge technologies and industry best practices.
- Improve scalability to support your business growth and changing market demands.
- Ensure compliance with industry regulations and data protection standards.
- Optimize costs by providing access to enterprise-grade IT solutions at a fraction of the cost of in-house implementations.
What Services do the Best IT Service Partners Offer?
Top IT service partners typically offer a comprehensive suite of services, including:- IT Infrastructure Management
- Cloud Managed Services
- Application Managed Services
- Data Managed Services
- Cybersecurity Managed Services
- Workforce Productivity Managed Services
What Factors Should You Consider When Comparing IT Service Providers?
When comparing IT service providers, consider the following factors:- Experience and Expertise: Look for providers with a proven track record in your industry.
- Service Portfolio: Ensure they offer a comprehensive range of Managed IT Services that align with your needs.
- Technology Partners: Check their partnerships with leading technology vendors.
- Support and SLAs: Evaluate their support structure, response time, and service level agreements.
- Security and Compliance: Assess their security measures and relevant industry certifications.
- Scalability: Ensure they can accommodate your growth and changing requirements.
- Pricing Model: Compare their pricing structures and ensure transparency in costs.
The Benefits of ITaaS
Switching from a traditional IT paradigm to ITaaS requires adjustments in an organization’s overall operations. However, by implementing ITaaS in a logical and controlled manner, organizations can ensure a smooth transition and long-term benefits. Following are some of the benefits: 1. Subscription-based Cost: One advantage of ITaaS is that it is relatively cost-effective. It is usually provided with a subscription-based payment structure to get as much service and support as you need to keep your teams functioning well. 2. Continuous and Proactive Monitoring: When businesses invest in ITaaS, they always have IT experts monitoring their systems for any symptoms of trouble — and intervening before things get out of hand, ensuring the safety of vital data. 3. Agility and Scalability: In contrast to traditional IT, which has extensive and rigid lead times, the ITaaS model helps businesses scale up and down as per their needs with flexibility. 4. Best Resources: Managed Services Providers (MSPs) have a vested interest in training their resources with the latest technical skills. When a business engages with an MSP for ITaaS, they can hire these skilled resources without investing in their hiring and training – for short and extended periods. 5. No Immediate Investment: ITaaS model allows businesses to start new technical projects without making exorbitant investments into hardware and other infrastructure requirements immediately.Common ITaaS Challenges
Customers and employees are becoming more demanding as firms become more reliant on technology, to the point where they expect the IT support services to be efficient, swift, and 24x7 available. However, for the ITaaS strategy to be successful, organizations must bring a shift in the mindset of all employees so that they can:- Think in terms of consumer business demands instead of focusing on hard assets
- Look at IT as a tool to enable business goals and not as the result
- Learn to challenge cultural barriers that hinder collaboration with external vendors
- Develop a fine mix of technical and commercial acumen
Synoptek’s ITaaS Services
Partnering with Synoptek can allow a firm to imagine a successful IT-driven future, alter existing operations, and evolve for long-term growth. Synoptek's ITaaS ensures that our client’s business operations are productive and effective while maintaining technological security and availability. We provide our clients with the best degree of service, which is responsive, thorough, and swiftly addresses their problems. Our services are tailored to our clients' short- and long-term requirements. Whether the client is looking for a partner to support their existing technology components or wants a consultant who can overhaul their enterprise environment, Synoptek's team is equipped to take on both these challenges. Our comprehensive ITaaS bundle includes the following services:- Managed Enterprise Application Support
- Managed Analytics and Reporting Services
- Managed Product Development Services
- Managed Cybersecurity Services
- Managed Cloud Services
- Managed Infrastructure Services
- Managed Workforce Productivity Services
What are the Key Services Offered by IT Managed Service Providers?
MSPs provide various IT services tailored to the specific needs of their customers. The most common ones include:- Network Monitoring: Continuous oversight of network performance and security.
- Data Backup and Recovery: Ensuring data integrity and availability through regular backups and disaster recovery plans.
- Application Management: Around-the-clock monitoring of critical business and custom applications to ensure high uptime, availability, and security.
- Helpdesk Support: Providing technical assistance to end-users.
- Cybersecurity Services: Implementing security measures to protect against threats.
- Cloud Services: Managing cloud infrastructure and applications.
How do IT Managed Service Providers Work?
The relationship between an organization and an MSP typically begins with assessing the current IT environment. This assessment helps identify areas for improvement and defines the services needed. After establishing SLAs, the MSP will implement monitoring tools, security protocols, and management processes tailored to the client's requirements and business goals.What are the Common Pricing Models Offered by MSPs?
MSPs usually charge clients through various pricing models:- Per Device: A fixed fee for each device managed.
- Per User: Charges are based on the individual users accessing the service.
- All-inclusive Pricing: A flat fee covering all managed services offered.
What are the Key Benefits of Using an MSP?
Managed IT services are in high demand now because technology service providers as well as the companies that rely on them, have learned, particularly during the pandemic, that implementing technology, managing it consistently, and efficiently running it while attempting to meet business goals is a complex and challenging task. Some of the benefits of using an MSP include:1. Defined Processes
MSPs have developed operational processes, integrated systems, automation, reporting, and organizational structures that allow them to successfully manage and advance technology at a high service level and with high quality. Many firms simply lack the necessary operational processes, systems, and personnel. As a result, businesses are increasingly turning to MSPs to outsource their technology operations.2. Skilled and Specialized Workforce
MSPs have a vested interest in learning and researching technology, staying on top of what's on the horizon, and keeping ahead of the competition. They offer experienced technical resources for a variety of technologies and services, and they use their technical experience to help their clients move their businesses forward with new and creative technology platforms, allowing them to stay ahead of competition and the market.3. Proactive Management
A decade back, technology service providers were waiting on the sidelines to manage when a client's technology failed. Today, "managing" technology entails more than just keeping systems up and running; it also includes efficiently adapting them to meet corporate needs. Managed services proactively ensure that a customer's technology ecosystem is always healthy and functional and that the client's business processes are consistently improving. The client pays for results with the new-age MSPs. They pay for the correct subject matter experts to assist them in making the most of their cloud technology, high service levels, responsiveness, and the assurance that their systems are not just up and running but also evolving.4. Better Management of Costs and Needs
MSPs' set fee structure assures consistent expenses month after month, avoiding large bill spikes or unanticipated investments, especially in difficult times. Furthermore, managed services providers enable expanding and even declining businesses to deal with seasonal unpredictability and scale up or down their services based on current requirements.The Roadblocks of Using an MSP
The complexity of bringing various technologies together to provide flexibility and variety continues to rise. As a result, businesses are looking for a single, dependable managed service provider who can support complex integrated settings while optimizing their technological expenditures. Information technology management as a service, often known as IT as a Service or ITaaS, is quickly becoming the de-facto norm for how businesses use and manage technology. As a result, selecting the correct MSP is more critical than ever. However, the biggest roadblock that organizations face during this shift is finding the right Managed Services Partner. A modern MSP must have the following qualities:- The latest technical capabilities
- A large and diverse staff with a wide range of capabilities to meet your requirements
- The size and scale required to assist you outside of business hours
- The capacity to work for a long period of time to maintain a high level of support
Selecting Synoptek as a Managed Service Provider
With the end goal in mind, Synoptek ensures that everything — your network, cloud, data, and applications – is secure and in sync. We oversee the entire technology lifecycle, and we do it using our tried-and-true paradigm for success, which eliminates unpredictability and ensures consistent results. We're big enough to scale with your needs as they change, yet small enough to go alongside you as a real partner on your digital transformation path. With Synoptek, you'll have a single point of contact for all of your IT needs, both now and in the future.What are the Benefits of Managed Security Services?
Managed security services providers (MSSP) offer 24/7 network and security monitoring, providing organizations with much-needed insight into who has been connecting to and accessing their network. By thoroughly monitoring enterprise networks 24/7, an MSSP will detect unusual entities lurking long before they launch an attack. In the event of an attack, the right MSSP will help execute the most effective response to a threat, minimizing the chances of hefty fines, poor business reputation, and lost customer trust. Through comprehensive firewall and antivirus management, a managed security services provider will ensure firewalls and antivirus solutions are properly configured and continuously patched. MSSPs regularly scan systems and software for vulnerabilities and recommend patches or other mitigations to address them. Some managed security service providers also offer advanced monitoring services to detect threats in real-time while managing and updating security policies across the organization.How is a Managed Security Service Provider (MSSP) Different from a Managed Services Provider (MSP)?
A managed services provider (MSP) assists organizations in managing and operating their IT infrastructure end-to-end. An MSP delivers various IT services across infrastructure, application, cloud, data, security, and workforce productivity. On the other hand, a managed security services provider focuses solely on the security aspects of infrastructure management. An MSSP offers a range of security support services, including cybersecurity consulting, cybersecurity assessment, risk analysis, application security consulting, vulnerability assessment, and security testing services.1. Should I Share an Overview of the Business?
A business overview is one of the first details to provide the MSP with the ability to build an IT optimization and savings roadmap. This includes the significant lines of business, the primary process, and the functional areas. These details will give the MSP deep insight into the nitty-gritty details of business while also helping it identify areas for savings. For instance, a comprehensive understanding of business and technology operations can help the MSP determine the technology maturity level and suggest steps to advance to the next stage of maturity to streamline operations and curb costs.2. Why are Details of Locations and Employees Important?
Furnishing details of business locations and the total number of employees at these locations is equally essential. For locations with a significant number of employees, an MSP can ensure higher availability, uptime, and scalability of critical systems while minimizing application sprawl across smaller locations with fewer resources.3. Does the MSP Need a Complete List of Critical Business Applications?
Yes. Providing a list of critical business applications, including their primary features, functions, and business areas that use them, can help enable substantial savings. This information will allow MSPs to craft a consolidation plan when combined with information about major third-party software, cloud platforms, and custom-developed applications. For instance, if different departments use different data analytics tools, the MSP can suggest consolidating these tools for better visibility and improved savings.4. How Will the MSP Use My IT Organization Chart?
Organizations must also share a comprehensive IT organization chart detailing full-time employees and contractors. Information about critical roles and responsibilities along with salary, bonus, and estimated benefits overhead can allow the MSP to determine duplicate resources or clashing responsibilities and provide recommendations for optimizing skill sets – and thus costs. For instance, if running and maintaining an in-house IT team becomes difficult, a qualified MSP can suggest outsourcing part or all IT services for long-term cost transformation.5. Do I need to Provide a Detailed List of IT Vendors?
If your organization depends on multiple vendors for multiple services, providing details about all services and their expenses is essential. From software licensing to vendor invoices, internal and external IT resource amounts to cloud consumption, application support, and more – MSPs can use this information to identify integration and interoperability challenges, determine opportunities for vendor consolidation, and streamline risk management.6. How Will Information About the Networking Environment Help?
An overall summary diagram or view depicting your total technology application landscape and networking environment can allow the MSP to understand their interconnectedness. The MSP can use this information to understand, monitor, and optimize the various network devices and take steps to minimize risk and prevent intrusions.7. Why do I Need to Disclose Information About the Data Organization?
Demonstrating how your organization obtains business insights from company data is critical to helping MSPs chart the right IT optimization and savings roadmap. A deep understanding of the technology platforms and business methodologies you use to build dashboards and reports can allow MSPs to understand your data organization and suggest tips and best practices to improve the quality and timeliness of insights. For example, suppose your organization struggles to get end-to-end visibility into specific processes. In that case, the MSP can suggest employing cloud analytics to produce a complete picture while curtailing the costs of expensive on-premises data analytics tools and systems.Enable Substantial Cost Savings Today
Today’s complex IT systems need continuous, around-the-clock monitoring by qualified experts. MSPs play a massive role in ensuring technology tools and applications work consistently, 24/7. But their purview isn’t just restricted to ensuring high uptime and availability. With the right MSP, organizations can also get assistance building a robust IT optimization and savings roadmap. Through a detailed understanding of your existing business and technology environment, a qualified MSP can help identify redundant tools and systems, optimize your IT infrastructure, and enable substantial cost savings along the way. The Synoptek Platform allows businesses to enjoy several benefits, including consistent IT operations, a stronger technology foundation, and substantial cost savings. Learn how the Synoptek Platform positively impacts organizations' IT and business strategy worldwide. Learn more about our extensive list of Managed Services through SynoptekMANAGE.Why are Managed Security Services Important?
Managed security services are crucial for organizations facing increasing cyber threats, as they provide access to specialized expertise and resources that may not be available in-house. By outsourcing security management, companies can leverage advanced technologies and skilled personnel to enhance their security posture, reduce risks, and ensure compliance with regulatory requirements. This approach often proves more cost-effective than building and maintaining an internal security team.What Services Do Managed Security Providers Offer?
Managed Security Providers (MSSPs) typically offer a range of services, including:- 24/7 Monitoring and Management: Continuous surveillance of networks and systems to detect and respond to threats in real-time.
- Threat Management: Identifying, analyzing, and mitigating potential threats before they can cause harm.
- Incident Response: Developing and executing plans to address security breaches or incidents swiftly and effectively.
- Compliance Monitoring: Ensuring that the organization meets industry regulations and standards related to data security.
How Do Managed Security Services Differ from Traditional IT Services?
Traditional IT service providers focus on general IT support and maintenance compared to managed service providers or managed security services providers (MSSPs), specializing in cybersecurity. MSSPs' primary mission is to protect an organization’s digital assets from threats, whereas traditional providers may not prioritize security in their service offerings. This distinction is essential for organizations whose primary concern is safeguarding their information systems.What Are the Benefits of Using Managed Security Services?
- Access to Expertise: Organizations can benefit from cybersecurity professionals' specialized knowledge and skills without hiring in-house staff.
- Cost Efficiency: Outsourcing security services can be more economical than developing and maintaining an internal security operation.
- Scalability: Managed security services providers can easily scale their services to meet an organization's changing needs, accommodating growth or shifts in security requirements.
- Proactive Threat Management: Continuous monitoring allows for early detection and response to threats, minimizing potential damage.
What is the IT Security Risk Management Strategy?
IT security risk management is the process of managing risks and threats associated with using information technology systems. IT security risk management strategy involves identifying risks, assessing risks, and implementing remediation and mitigation techniques to safeguard the confidentiality, integrity, and availability of organizational data assets. Implementing an effective IT security risk management strategy requires the right combination of people, processes, and technology.What are IT Network Management Services?
IT network management services encompass a range of functions that organizations outsource to effectively oversee, monitor, and maintain their network infrastructure. These services are typically provided by managed service providers (MSPs) and are designed to optimize network performance, enhance security, and reduce operational costs.How Do I Choose a Managed Security Services Provider?
When selecting an MSSP, consider the following criteria:- Experience and Reputation: Look for providers with a proven track record and positive client testimonials.
- Service Offerings: Ensure the MSSP offers a comprehensive service suite that aligns with your organization's security needs.
- Technology and Tools: Evaluate the providers' technologies and tools for monitoring and threat detection.
- Customization and Flexibility: Choose a provider that can tailor their services to fit your specific requirements and adapt to changes over time.
What is the History of Managed IT Services?
Managed IT Services emerged in the late 1990s as businesses outsourced their IT needs. Initially, companies sought help with basic IT management tasks but Managed IT Service Providers now offer a wide range of solutions, from proactive monitoring to cloud services and more. Today, Managed IT Services provide comprehensive and flexible support which is crucial for the efficient functioning of modern-day businesses.What is the Managed IT Services Model?
The Managed IT Services model revolutionizes how businesses handle their technology needs. Providers deliver comprehensive IT support, from setup to monitoring and proactively assessing infrastructure for threats and enhancements. Offered at flat, tiered rates, clients choose service levels tailored to their needs with the flexibility to adjust as their business evolves. By providing affordable software-as-a-service (SaaS) solutions, Managed IT Services enable partners to streamline their business operations and increase efficiency.What is Included in Managed IT Services?
Managed IT Services offer comprehensive support for an organization’s technology infrastructure. These services include monitoring, maintenance, cybersecurity, software updates, cloud management, data backup, help desk support, and IT consulting. SLAs ensure timely issue resolution and scalability for evolving business needs.What is the difference between Managed IT Services and Outsourcing?
Outsourcing is the allocation of IT tasks to an external service provider. It generally comprises utility services, software as a service, and cloud-enabled outsourcing and helps organizations reduce costs and accelerate time-to-market. Managed Technology Services deals with the end-to-end management of technology-related tasks to a skilled and competent partner. They enable a more holistic and comprehensive approach to technology management and offer vital strategic advice on potential risks, challenges, and areas of improvement. With a high degree of oversight, they enable the development of a technology roadmap that is effective, long-lasting, and built in the interest of the business.Are Managed IT Services the Same as SaaS?
While SaaS provides companies with software that they can use over the cloud, Managed Technology Services go a step further. They encompass a range of technology support services that span different networks, devices, and applications and help organizations leverage their technology systems most effectively.What are the Benefits of Managed IT Services?
Managed IT Services offered by a proficient Managed Services Consulting company can help businesses cut costs, shorten time to market, and get access to external expertise, assets, intellectual property, and other benefits. Here are the top 4 benefits of Managed IT Services:1. Reduced Expenses
When you partner with a competent Managed Services company, you benefit from significant cost reductions, including reduced personnel compensation and lower infrastructural and operational costs.2. Significant Time Savings
Partnering with a Managed Services Consulting company can help cut the time and costs of advertising, interviewing, selecting, and training new in-house staff. Instead, you can leverage the skills and competence of IT experts who are well-versed with the latest trends and best practices.3. Access to a Global Talent Pool
Outsourcing Managed Services to an expert Managed Services Provider allows you to reach out to professionals globally who may be in short supply or unavailable locally. It enables easy, on-demand access to extensive world-class resources to meet unique business and technology needs.4. Uninterrupted Workflow
Managed IT Services also allow you to run your business around the clock – thanks to 24/7 support by certified experts and the presence of a global delivery model.What are the Different Types of Managed IT Services?
The support and management of any technology or service area can be a candidate for Managed IT Services. However, here are the top service areas:1. IT Infrastructure Managed Services
IT Infrastructure Managed Services help monitor and support IT systems, applications, and infrastructure 24/7. They enable organizations to focus on driving their business forward and not worry about the day-to-day management of the technology foundation that keeps their business running.2. Application Management Services
Modern applications require continuous management throughout their lifecycle. Application Managed Services help organizations support and maintain the performance and functionality of their applications. Organizations can improve application uptime, scalability, and security by resolving incidents to responding to user requests requiring specific product knowledge and expertise and using the best tools and strategies.3. Data Managed Services
As organizations continue to collect humongous amounts of data, managing and maintaining these datasets has become a global challenge. Data Managed Services help organizations efficiently manage organizational data while keeping up with the volume of data growth. They also aid in cleansing and storing data, analyzing it for insights, and helping organizations make evidence-based business decisions.4. Cloud Management Services
As the cloud lays the foundation of digital transformation initiatives, planning the migration, managing resources, and ensuring availability while optimizing cloud costs isn’t easy. Cloud Management Services enable organizations to leverage a comprehensive suite of expert services to streamline day-to-day cloud management. They also help maintain cloud functionality, address security and privacy concerns, and boost cloud ROI.5. Workforce Productivity Managed Services
As the global workforce gets increasingly hybrid, managing and empowering geographically dispersed employees is a challenging task. Workforce Productivity Managed Services set the foundation for an interconnected and interoperable workplace of the future. With the implementation and regular management of modern productivity tools, these services can eliminate silos and help organizations re-imagine collaboration between cross-functional teams while maintaining the highest levels of security and functionality.6. Cybersecurity Managed Services
Technology advancements have made the cybersecurity landscape extremely vulnerable to attacks. Cybersecurity Managed Services aid organizations in establishing the right cybersecurity controls and policies across networks, servers, applications, users, and secondary devices. Via continuous monitoring, they help strengthen enterprise security while enabling companies to keep pace with the rapidly evolving threat landscape.What is the Impact of Managed Services on In-house IT Teams?
Opting for Managed Services can enable your internal IT team to focus on more strategic initiatives that can drive your business forward. This can help increase your organization’s efficiency and enhance your ability to offer better customer service. By partnering with a Managed IT Provider, you can proactively mitigate potential disruptions rather than relying on your internal team to react to emergencies. Essentially, you can avoid the wait-and-fix approach and instead focus on preventing issues from arising in the first place.Are Managed IT Services Cost-Effective?
Managed IT Services lead to significant cost savings. However, the actual cost depends on various factors such as the location of the Managed Services provider, the level and variety of services opted for, your security and compliance requirements, level of communication and collaboration, delivery model, billing cycle, SLAs (service-level agreement), and support metrics.What is a Managed Service Provider (MSP)?
A Managed Service Provider is a specialized third-party organization that delivers and oversees IT services and infrastructure for businesses. MSPs assume complete responsibility for managing and maintaining defined technology services for their clients, delivering these services proactively based on comprehensive SLAs. They provide ongoing monitoring, management, and problem resolution for the systems within their scope of services. MSPs typically operate on a subscription-based model, offering various service tiers to accommodate different business needs and budgets. Organizations can delegate their IT operations by partnering with an MSP while focusing on core business objectives and strategic initiatives.Leveraging SynoptekMANAGE
At Synoptek, we understand that after the initial evaluation and implementation of technologies, consistently managing them and running them efficiently while meeting business goals is a complex and challenging task. SynoptekMANAGE comes bundled with tried-and-tested plans to help you protect your enterprise, optimize human and technology resources, and grow by maturing processes and capabilities. As a skilled Managed Services Provider, our offering helps you redefine your operational processes, integrate systems, optimize automation, and create reporting mechanisms. The ultimate goal of SynoptekMANAGE is to enable you to effectively manage and evolve technology in a high service level, high-quality manner. Speak to our managed services experts to learn more.Managed Cloud Services Benefits
Organizations that envision a technology-centric future and want to transform their businesses using IT as a catalyst should work with a knowledgeable and competent Cloud MSP. The following are the top advantages of working with a Cloud MSP:- Expertise available on-demand: You get on-demand access to experienced and skilled professionals with deep domain knowledge. These experts then provide timely strategic consultation and implement a proven set of processes to help you reach your goal.
- Exceptional cost-savings: When you choose a Cloud MSP, you don't have to invest time and money in looking for professional cloud-skilled talent, hiring, and upskilling them.
- Business resilience and agility: You may achieve high levels of business agility and resilience by working with a cloud MSP. Since the MSP typically has a solid network infrastructure with round-the-clock management, you can count on them to monitor, scan, and upgrade your ecosystem.
- Support for cybersecurity: Since the MSP has a complete understanding of your cloud infrastructure and has up-to-date information on current threats, you can be rest assured that the risk of sensitive and vital data being stolen by hackers and other cybercriminals is minimal.
Working with a Managed Cloud Service Provider
Business expansion today necessitates the use of cloud computing. However, to get optimal services from the MSP, you must:- Choose the right vendor with proven expertise in your industry vertical
- Ensure that the chosen MSP has enough resources to scale your environment and provide 24x7 support
- Collaborate with the MSP at each step of your cloud journey
Why Consider Synoptek as a Managed Cloud Services Provider
Security, privacy concerns, and short/long-term functionality which might prevent hyperscale cloud adoption, are addressed and solved by Synoptek's managed cloud services. Our managed cloud services are one of the best solutions available in the independent cloud services sector – ideal for enterprises looking for a completely trouble-free and safe cloud experience. To know more about Managed Cloud Services by Synoptek, click here.What are the Key Benefits of Managed IT Services in Healthcare?
Key benefits include:- Cost savings: Reduces the need for in-house IT staff and infrastructure.
- Improved patient experience: Enhances service delivery through efficient IT systems.
- Data security: Protects sensitive patient information with robust cybersecurity measures.
- 24/7 support: Ensures continuous operation and quick issue resolution.
How do IT Services Enhance Healthcare Security?
Healthcare Managed IT Services partners improve healthcare cybersecurity by implementing advanced security protocols, conducting regular system monitoring, and ensuring compliance with regulations like HIPAA. They provide ongoing threat detection and incident response to protect sensitive data from breaches.What Types of Medical Institutions can Benefit from Healthcare IT Services?
Managed IT services for healthcare can benefit organizations of all sizes, including hospitals, clinics, and specialized practices. Healthcare IT managed services providers (MSPs) are particularly advantageous for organizations looking to optimize their IT operations without incurring significant costs associated with maintaining an in-house team.How do I Choose a Managed IT Services Provider for Healthcare?
When selecting a provider, consider factors such as:- Experience: Look for providers with a proven track record in dealing with EHRs, EMRs, HIMs, etc.
- Service offerings: Ensure they provide comprehensive services tailored to your needs.
- Compliance knowledge: Verify their understanding of healthcare regulations.
- Support availability: Check for 24/7 support capabilities.
What Challenges do Healthcare IT Managed Service Providers Address?
Managed IT service providers (MSPs) help tackle several challenges including:- Rising costs: Provide cost-effective solutions to manage complex IT systems.
- Staffing issues: Reduce the burden of recruiting and retaining skilled IT personnel.
- Compliance management: Ensure adherence to stringent healthcare regulations.
How do MSPs Improve Patient Care?
Managed IT Services for Healthcare significantly improve patient care, enhance operational efficiency, streamline data management, and improve communication. Here are the relevant ways these services contribute to better patient outcomes:- Streamlined access to patient information
- Enhanced communication and collaboration
- Remote consultations and telemedicine
- Real-time monitoring and alerts
- Improved data security and compliance
- Proactive maintenance and support
- Automation of routine tasks
- Data-driven decision making
How Can Managed IT Services Help with HIPAA Compliance?
Managed IT services are essential for helping clinical organizations maintain HIPAA compliance by providing expert guidance on regulations, conducting thorough risk assessments, and implementing robust data security measures such as encryption and firewalls. Providers also ensure regular software updates and patch management to mitigate vulnerabilities, protect patient data, and reduce human errors.How do MSPs Handle Data Security?
Managed IT service providers ensure data security by implementing robust security measures such as firewalls, encryption, and intrusion detection systems to protect sensitive patient information. With regular security audits to identify vulnerabilities to ensure HIPAA compliance, healthcare IT managed services provide comprehensive disaster recovery plans to restore data in case of breaches quickly, secure network management to prevent unauthorized access, and continuous monitoring to detect security incidents in real time. Such strategies allow healthcare organizations to focus on patient care while safeguarding critical data. Are you looking to engage with a managed services provider for your healthcare center in Orange County? As an award-winning, globally trusted technology consulting and managed service provider (MSP), we offer a comprehensive range of healthcare IT services. Contact our Orange County managed services experts to learn more.Why do You Need Application Managed Services?
Is application management suitable for you and your company? Here are a few compelling reasons to help answer this question:1. You Want to Save Money, Time, or Both
Application management services help save two things, money, and time. By entrusting your applications and IT infrastructure to a skilled application management services provider, you free teams to address other critical issues. With efficient professionals on the job, you get more for your dollar.2. You need Specialists
Maintaining complex IT infrastructure necessitates hiring many specialists with deep knowledge and experience of managing diverse applications across different languages, operating systems, devices, and technologies.3. You are Experiencing a lot of Change
In the technology world, change is the only constant. Since new applications, features, and technologies must constantly be adopted, with an Application Managed Services provider in tow, competent resources will automatically handle all aspects.4. You Have to Measure Performance
A qualified Application Management Services team can track the performance, functionality, storage, and other aspects of your web and mobile apps. These metrics can be used to ensure that your applications are working as expected, identify areas for improvement, and suggest steps to ensure your performance goals are met.What are the Benefits of AMS?
- Innovation: Application Managed Services guarantee that applications are well-managed, allowing internal teams to devote more time to new ideas, make crucial business choices, and provide support in a more timely and effective manner.
- Increased performance: Application Management Services improve performance by synchronizing design, development, and testing efforts and reducing maintenance.
- Business continuity: Application Management Services lower the risk of IT and other downtime for your company and customers. The team also applies best practices when creating and implementing systems, which helps boost efficiency. This helps your firm stay focused on what it does best.
- Total cost of ownership: Application Management Services improve flexibility by reducing the time taken to develop and deploy apps. Fewer IT staff is required to handle problems, allowing teams to improve efficiency while lowering operating costs. Constant fine-tuning can also eliminate poor performance and reduce overall service costs.
Why Should You Consider Synoptek’s Application Managed Services?
Synoptek, a leading AMS Provider, offers Managed Application Services that include management, monitoring, and proactive maintenance to ensure that your ERP, CRM, and e-commerce systems can deliver faster business results. We adopt a revolutionary approach to Application Managed Services, ensuring that you stay relevant and updated in today’s competitive business environment by constantly striving for ongoing improvement, innovation, and optimization. Our key Managed Application Support and Maintenance Services include:- Ongoing Monitoring and Maintenance
- User Management and Access Control
- Disaster Recovery and Business Continuity
- Vendor Management
- 24×7 Helpdesk Support
How Can Organizations Achieve Cost Savings Through Strategic IT Spending?
To maximize cost savings, your company should start with the following steps:1. Prioritize IT Budgeting
Effective budgeting involves categorizing expenses into capital, project, and operating costs. By analyzing previous spending and setting clear objectives, organizations can identify areas for potential savings and avoid overspending on unnecessary services.2. Leverage Managed Service Providers (MSPs)
Utilizing Managed Service Providers (MSPs) for network management and cybersecurity is a cost-effective option cost than maintaining these functions in-house. They provide predictable monthly expenses, eliminating unexpected costs associated with traditional IT management.3. Eliminate Redundant Resources
Regularly assess existing IT assets to remove redundancies. This can streamline operations and reduce maintenance costs, allowing you to focus their budgets on essential technologies.4. Implement Zero-Based Budgeting
This method requires justifying every line item in the budget from scratch rather than basing it on previous years' spending. You can cut unnecessary expenditures by evaluating the necessity and alignment of each project with business goals.What Role do Managed Service Providers (MSPs) Play in Achieving Service Level Excellence?
MSPs help organizations maintain high service levels by:- Providing Expertise: MSPs have specialized knowledge and expertise that can enhance service delivery without requiring extensive in-house training or hiring.
- Ensuring Compliance: Managed service providers help organizations adhere to industry regulations, compliance requirements and standards, reducing the risk of costly penalties or downtime due to non-compliance.
- Enhancing Security: With cybersecurity threats rising, MSPs offer robust security solutions that protect sensitive data and maintain operational integrity.
What should Organizations Consider When Selecting an MSP?
When choosing an MSP, organizations should evaluate:- Service Level Agreements (SLAs): Clear SLAs define performance expectations, including response times and uptime guarantees, ensuring accountability from the provider.
- Alignment with Business Goals: The MSP's services should align with the organization's strategic objectives to maximize the return on investment.
- Scalability of Services: As businesses grow, their IT needs change. An effective MSP should offer scalable solutions that can adapt to evolving requirements.
How Can Organizations Measure the Effectiveness of Their IT Spending?
Organizations can assess their IT spending effectiveness by:- Tracking Key Performance Indicators (KPIs): Metrics such as system uptime, incident response times, and user satisfaction scores can provide insights into how well IT investments perform against expectations.
- Conducting Regular Reviews: Periodic evaluations of IT expenditures against business outcomes help identify areas for improvement and ensure alignment with strategic goals.
- Benchmarking Against Industry Standards: Comparing spending levels and service quality with industry peers can highlight opportunities for optimization.
What Trends are Shaping the Future of IT Spending?
The landscape of IT spending is evolving with several key trends:- Increased Focus on Cybersecurity: As cyber threats grow more sophisticated, organizations prioritize investments in security measures to protect their assets.
- Adoption of Cloud Solutions: Many businesses are shifting towards cloud-based services for flexibility and cost efficiency, further driving the need for strategic IT planning.
- Emphasis on Digital Transformation: Organizations are investing in digital initiatives to enhance customer experience and operational efficiency, necessitating a re-evaluation of traditional IT budgets.
What is the Difference Between Managed Services and Outsourcing?
Managed services involve a strategic partnership with a third-party provider that proactively manages an organization's IT infrastructure and operations. Managed IT services providers offer a range of technology-focused services across IT consulting, business applications support and management, data engineering, workforce productivity, product development, cloud computing, cybersecurity, etc. IT outsourcing involves hiring a third-party provider to perform services traditionally performed in-house. IT outsourcing partners often provide a 24/7 helpdesk to streamline and simplify the issues users face in their day-to-day tasks.What is Typically Included in the Scope of Managed IT Services Providers and IT Outsourcing Partners?
Managed IT services often include ongoing support, maintenance, and monitoring of an organization’s technology systems. Instead of being specific to a particular department or system, managed IT services providers focus on the end-to-end management of the IT environment, helping customers meet their business goals. IT outsourcing is often project-based, where specific tasks are contracted to an external provider. These can range from software development to technical support, infrastructure management, etc.What Aspects do Managed IT Services Providers and Outsourcing Partners Focus On?
Managed IT services providers emphasize long-term partnerships and focus on improving technology efficiency, application uptime, and enterprise security. IT outsourcing partners typically focus on resolving IT issues users face daily while reducing costs and maintaining application performance and functionality.How do the Roles and Responsibilities of Managed IT Services Providers and Outsourcing Partners Differ?
With managed services, the MSP is responsible for outcomes and performance. MSPs agree on pre-defined SLAs with the customer organization and are required to deliver services based on the terms in the contract. With outsourcing, responsibility may be shared or may also be with the customer organization. While IT outsourcing partners also agree on SLAs, there is far more customer oversight in delivering services.What are the Differences in Cost Structures Between Managed IT Services and IT Outsourcing?
MSPs usually offer services via predictable, subscription-based pricing. Customer organizations can choose from a range of managed IT services and pay for the services they use annually. IT outsourcing partners often charge customer organizations on project scope or hourly rates. Some also use a fixed-price model for projects with well-defined requirements and timelines.1. I'm Considering Completely Outsourcing the Day-to-day Management of My Growing Technology Landscape to a Managed Services Partner (MSP). How Does this Approach Typically Work?
Complete outsourcing involves transferring all your IT responsibilities to an MSP, which manages and maintains all IT infrastructure, applications, and services. This approach can provide significant cost savings and allow your company to focus on core business activities. To ensure a successful partnership, you must carefully evaluate the MSP's expertise, infrastructure, and service level agreements (SLAs). Look for an MSP with a proven track record of managing complex IT operations and a comprehensive SLA that outlines the scope of work, service levels, and performance metrics.2. How Can Partial Outsourcing Help My Company Achieve its Goals, and What are the Key Considerations?
Partial outsourcing involves outsourcing specific IT functions or services, such as 24x7 help desk support, network management, or cloud services, while retaining control over other IT operations. This approach can benefit companies that want to maintain reigns over some of their IT operations while achieving cost savings and improved efficiency across others. When evaluating partial outsourcing options, it is essential to assess the MSP's expertise and infrastructure to ensure they can handle the specific services you're outsourcing.3. What are the Critical Differences Between Offshoring and Outsourcing, and How Do I Choose the Right Approach for My Company?
Offshoring involves transferring IT operations to a different country or geographic region to take advantage of lower labor costs. Contrarily, outsourcing involves transferring IT operations to a third-party vendor within the same country or region. Offshoring can provide significant cost savings but presents additional challenges, such as cultural and language barriers and potential security risks. When evaluating offshoring options, it's essential to consider these factors carefully and ensure that the MSP has the expertise and infrastructure to manage IT operations effectively.4. What is a Blended Approach, and How Does it Combine Different Outsourcing Models?
A blended approach combines different outsourcing models, such as partial and offshoring, to achieve a customized solution that meets your company's needs. For example, a company might outsource help desk support to a local MSP while offshoring network management to a provider in a different country. When evaluating blended approaches, consider the IT functions or services that would benefit from outsourcing and the potential benefits and risks associated with each approach. It is also essential to assess the MSP's expertise and infrastructure to ensure they can handle the specific services you're outsourcing.5. What is Employee Transition or Rebadging, and How Does it Work?
In the context of outsourcing, employee transition or rebadging can occur when employees currently working for the client company are transitioned to become employees of the MSP. The MSP then assumes responsibility for managing these employees, including their payroll, benefits, and day-to-day work assignments. This type of transition often occurs when the client company outsources specific functions or departments to the MSP. It depends on various factors, such as the outsourcing model, contractual agreements, legal and regulatory considerations, and the strategic objectives of both parties. If you rebadge your employees, you will realize cost reduction, staffing flexibility, and smooth customer journeys. It is a win-win situation for both, ensuring business continuity for clients and employee career opportunities.6. What are the Critical Considerations for a Successful Transition Process, and How can I Ensure Minimal Disruptions?
The transition process typically involves several stages, including planning, execution, and post-transition support. During the planning stage, the MSP will work closely with your company to understand its IT operations, identify areas for improvement, and develop a customized transition plan. During the execution stage, the MSP will transfer IT operations, including employee training and onboarding. Post-transition support ensures that any issues or concerns are addressed promptly and efficiently. By following a structured transition process, your company can minimize disruptions and ensure a smooth transition to the MSP. It would be best to consider the MSP's expertise, infrastructure, and transition plan for evaluation. Establishing clear communication channels and ensuring all stakeholders are informed and prepared for the transition is also essential.Maximize Technology Results with the Right Provider
Successful companies have found that upstream work during the outsourcing strategy, negotiations, and transition phases sets the foundation and can significantly impact the price and service delivery outcome. By carefully planning and executing these critical steps, you can ensure that outsourcing partnerships deliver the desired results. With established business models, processes, strategic approach, global collaborations, and consistent evaluation, we at Synoptek can help you leverage technology to maximize your efficiency and suit your business with significant cost savings. Learn more about our entire gamut of managed services called SynoptekMANAGE here.- Expertise and Experience: Look for a managed IT services provider with experience in your industry and expertise in the technologies relevant to your business needs.
- Customization: Choose an IT Services partner who can tailor solutions to meet your business goals.
- Scalability: Seek an IT support services partner capable of scaling services and delivery models as your user base expands and your market requirements grow.
- Security and Compliance: Engage with a Managed IT services partner who is strongly committed to data security and regulatory compliance.
- Support and Communication: When selecting an IT services partner, it is essential to evaluate customer support structure, SLAs, and overall responsiveness to issues and concerns.
Why is Choosing the Right IT Services Partner Important?
Choosing the right managed IT services partner can help unleash your organization’s full potential by:- Reducing risks by studying your entire IT environment, identifying known and unknown risks, and mitigating them effectively.
- Keeping up with the pace of change by helping you fully leverage the technology you’ve invested in to drive unrivaled ROI and tangible, measurable business results.
- Maintaining security by fortifying your systems against potential threats, adopting the latest security tools and processes, and maximizing security according to industry best practices.
- Evolving and adapting your business to new market and customer expectations by constantly advancing your technology environment.
- Driving high customer satisfaction scores pinned by support models that enable responsive and proactive support and deliver the customer service levels you desire.
What Should You Keep in Mind While Seeking a Managed IT Services Partner?
With hundreds of managed IT service partners in the market, choosing the right one can be challenging. Here are some things to keep in mind:- Local presence: Having an IT services partner with a local presence is essential to get immediate support and assistance for critical IT needs. For instance, if you are based in Denver, partnering with a managed service provider (MSP) in Denver can help make your technology environment an asset rather than a liability, so you can focus on achieving your strategic business objectives.
- Global delivery: Besides local presence, looking for an IT services partner with a global delivery model is essential. This can enable access to global talent, ensuring 24/7 support, improved service quality, and reduced operational costs – regardless of the location or time zone.
- Operational flexibility: Opting for a managed IT services partner that provides technology-agnostic and vendor-lock-in free services is equally important. Such a partner can allow you to switch providers while staying within your budget and timeline constraints.
- Experience: Look for MSPs with a proven track record in your specific industry. Check if the MSP has relevant certifications to demonstrate their technical proficiency and commitment to best practices.
- Range of Services: A good MSP should provide a wide array of services, including network management, cybersecurity, data backup, and compliance support. Choose the one that offers tailored solutions that align with your business goals.
- Service Level Agreements (SLAs): Ensure that the MSP provides detailed SLAs outlining service scope, uptime guarantees, response times, and resolution procedures.
- Customer Support: Evaluate your MSP’s customer service responsiveness. A good MSP should offer 24/7 support and have a clear escalation process for issues that arise.
- Technology and Tools: Your chosen MSP should utilize current technologies and tools to manage your IT infrastructure efficiently. Look for providers who stay ahead of trends and can offer innovative solutions that enhance your business operations.
- Cost Structure: Understand the MSP’s pricing structure—whether it’s per device, per user, or all-inclusive—and ensure there are no hidden costs.
What are the Key Qualities to Look for in an IT Managed Service Provider?
When selecting an IT Managed Service Provider (MSP), certain qualities can significantly impact your business's operational efficiency and success. Here’s what you need to consider:- Technical Expertise: A proficient MSP should have strong technical knowledge and experience in managing various IT environments.
- Proactive Management: A good MSP actively monitors systems to prevent problems before they arise. Skilled MSPs maintain system integrity and performance with regular system checks, updates, and cybersecurity measures.
- Transparency: Your MSP should provide clear insights into their processes, including detailed reports on service performance and ongoing activities.
- Scalability: As your business grows, your IT needs will evolve. A reliable MSP should offer scalable solutions that can adjust to your changing requirements without disrupting service quality or incurring unnecessary costs.
- Security Measures: To combat increasing cyber threats, your MSP should implement advanced security measures, including regular testing and monitoring, to protect sensitive data from breaches.
- Proven Track Record: Look for an MSP with a solid reputation backed by positive client testimonials and case studies.
What are the Common Pitfalls When Choosing an MSP?
Selecting the right Managed Service Provider (MSP) is crucial for the smooth operation of your IT infrastructure. However, many organizations fall into common traps during this process. Here are the key pitfalls to avoid:- Not Verifying Certifications: Failing to insist on certified technicians and vendor solutions can lead to hiring unqualified providers.
- Settling for Limited Support Options: Some MSPs may offer only remote or on-site support, which can be inadequate for your needs.
- Overlooking Compliance Requirements: Neglecting to confirm that your MSP can maintain compliance with relevant laws can expose your organization to legal risks and penalties.
- Choosing Inexperienced Providers: Opting for an MSP that lacks experience in your specific industry can result in generic solutions that fail to address your unique needs.
- Ignoring Communication and Engagement: If an MSP seems disinterested or fails to ask insightful questions about your business challenges, it may indicate a lack of commitment to providing customized solutions.
- Focusing Solely on Price: Choosing an MSP based solely on cost can backfire. A low price often correlates with lower service quality. Evaluate the overall value offered by the MSP, including their expertise and range of services, rather than just the price tag.
IT Outsourcing Types
There are two main forms of IT outsourcing, each defined by how the IT work is outsourced. Project Based Outsourcing: For this arrangement, an organization gives the external outsourcing provider all project-related information, and the outsourcing provider handles all software development, quality assurance, and project management. Managed Services Based Outsourcing: In the managed services approach, the organization buys staff hours from an IT outsourcing provider. Typically, the outsourcing provider is paid hourly or monthly rates for the outsourced staff.The Pros of IT Outsourcing Services
The benefits of IT outsourcing are numerous; let's look at the top eight advantages of IT outsourcing:- Expert resources to manage all your devices, networks, and cloud services
- Optimal performance and stability of your IT systems, as well as access to monthly reports on your IT environment's current state
- High availability, dependability, and uptime of your IT infrastructure with minimal outages
- Improved IT efficiency through standardized operations and optimized processes
- Cost savings in the areas of capital expenditures, support and management, and training
- Predictable spending with an as-a-service approach in which you pay monthly set prices for the services you utilize
- Management of on-premises systems, cloud applications, and other vendor goods from start to finish
- Improved security posture through comprehensive management of endpoints, firewalls, networks security, and compliance
Why You Should Consider IT Outsourcing Services
A well-planned technology setup gives any business a competitive advantage by making in-house collaboration and communication seamless. Experienced IT outsourcing firms help businesses relook at their internal tech setup and align it to their bigger business goals. A good technology partner will help their client:- Implement and manage a fast-expanding array of technologies in today's ever-evolving business world
- Create business value by rethinking how you do business with technology
- Boost productivity by allowing cross-company collaboration and communication
- Provide excellent client service
- Enable a security program and secure its data
- Tailor frameworks and processes to each initiative's requirements
IT Outsourcing Services at Synoptek
Synoptek is a leading Global IT Outsourcing services provider. We help our clients envision a successful IT-driven future, transform existing operations, and evolve for long-term growth. Our Global IT Outsourcing services include proven strategies that help businesses safeguard their information, leverage people and technological resources, and mature procedures and capabilities. Our services assist businesses in redefining operational procedures, integrating systems, automating operations, and developing efficient reporting methods. Our goal is to enable our clients to successfully manage and evolve technology while maintaining a high level of service and quality. Our comprehensive services bundle helps clients with all their technology needs, which means they do not have to juggle between multiple vendors. Our IT outsourcing services include:- Managed Enterprise Application Support
- Managed Analytics and Reporting Services
- Managed Product Development Services
- Managed Cybersecurity Services
- Managed Cloud Services
- Managed Infrastructure Services
- Managed Workforce Productivity Services

- Takes care of your website's visual branding
- Handles all your mobile app's Web/Android/iOS upgrades
- Keeps applications available, dependable, and relevant to changing business requirements
- Focuses on application stabilization, service optimization, and application improvement
- Involves functionality growth and modification, troubleshooting, and the creation of supplemental solutions
What are the Benefits of Application Support and Maintenance?
Now that you are aware of the importance of Application Support and Maintenance, you should also know about its advantages. Here are a few examples:- Scalability and Security: Maintaining your application regularly ensures safety from all external threats while making them more scalable. It enables higher workload accommodation and helps in maintaining consistent and acceptable performance levels.
- Cost-cutting: Buying new software or developing it from scratch whenever it crashes or develops bugs is not a cost-effective strategy. Supporting and maintaining apps is a far better way to enhance their lifetime and reduce future costs.
- Customer Satisfaction: Maintaining applications and websites improves their quality, web presence, and response time. It evolves the company over time and fulfils customer requirements better, resulting in improved satisfaction levels.
- Peace of Mind: Knowing that your apps are constantly supported and monitored for issues and improvements delivers immense peace of mind, allowing you to focus on other, more strategic aspects of your business.
What are the Challenges of Application Support and Maintenance?
Here are few challenges organizations face when it comes to efficient Application Support and Maintenance:- Developing a long-term, cost-cutting approach to reduce ownership and support expenses
- Constantly customizing applications to satisfy the needs of changing business environments
- Dealing with insufficient documentation of existing applications
- Navigating through a massive IT portfolio of inflexible and unnecessary systems
- Constantly striving to accomplish the highest quality standards while supporting and maintaining applications
Why Opt for Synoptek’s Application Support and Maintenance Services?
No legacy can last forever; it is essential to know when to upgrade. That is why Application Support and Maintenance is necessary, and you need a professional to do that. Synoptek provides various Application Support and Maintenance Services to help you maintain the quality, availability, security, and speed of your applications throughout their lifecycle, from conception to planning, design, development, maintenance, support, and retirement. Our Application Support and Maintenance services are tailored to get the most out of your software.- Support and Enhancements: Leverage Synoptek’s expert team for ongoing application enhancement, performance monitoring and tuning, preventive, and proactive software maintenance, and SLA-driven software support.
- Real-time Support (Helpdesk Assistance): Leverage our 24x7 technical support with a helpdesk ticketing system. Our seasoned team members deliver prompt assistance with streamlined support processes.
- Application Upgrade and Monitoring: With our upgrade and monitoring services, we ensure that all your platform upgrades are done on-time, and there is zero or minimal downtime in your environment.
- Customer Success Services: Engage our expert team members with deep knowledge of the product and domain to onboard clients and manage product customization, product configuration, data processing, and report creation.
- Re-platforming
- Rehosting
- Recoding
- Re-architecting
- Replacing
- Retiring
- Operating systems at an optimal level without causing any performance or security disruptions
- Enhancing the scalability of the enterprise ecosystem
- Reducing the maintenance and support cost of the applications in the cloud
- Leveraging the latest security features
- Empowering the workforce with the latest technology so that they can focus on mission-critical tasks rather than spending time resolving the endless list of application-related issues
- Define the modernization strategy with a futuristic approach
- Define business objectives, requirements, priorities, and outcomes at the onset
- Decouple components and approach the project by function
- Have a data migration checklist in place
- Never lose focus from performance and user experience
- Allow time to train users on the new application
How Can Synoptek Support an Organization’s Application Modernization Strategy?
Synoptek's App Modernization strategy is straightforward. We:- Evaluate the legacy application
- Identify risks and vulnerabilities
- Provide clear guidelines on how to go about application modernization
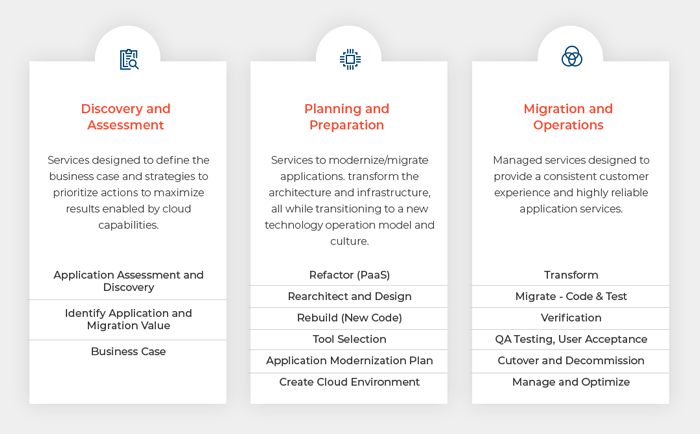
- Redesign applications
- Rewrite them using the newest technologies and design patterns
- Combine numerous apps into one for better performance and scalability
Best Practices for IT Cost Optimization
Many businesses regard cost optimization as a one-time task that yields measurable financial rewards. Approaching organizational cost savings in this way is doomed to fail in the ever-changing technology world. A new, more strategic approach, called Cost Transformation, promises to produce better results that result in real cost reductions while also preparing a company to succeed in the future.Cost Transformation Provides a More Productive ‘Cost Optimization’ Path
Rather than merely looking for ways to cut technology expenses, a strategic cost transformation approach starts by reviewing an organization's business objectives. A strategic cost transformation program is guided by three primary ideas:- Reducing costs across any declining business areas to stabilize the company
- Getting the most out of every dollar spent by creating an elastic subscription model and continuously adjusting costs to react to seasonal demands
- Creating a growth-oriented investment engine to help the company benefit from new technology and business opportunities
IT Cost Optimization Challenges
Despite careful planning, cost-optimization attempts continue to result in IT overspend. This can occur due to a variety of reasons, including the following:- Focusing on short-term goals rather than establishing long-term and sustainable cost-cutting methods
- Focusing solely on headcount reduction without a clear grasp of how it will influence all aspects of the organization
- A lack of awareness amongst stakeholders about the role of IT infrastructure in business processes
- Lack of senior and middle management buy-in
- Sweeping, abrupt cuts with improbable saving targets
- Inefficient performance tracking tools
Synoptek’s IT Cost Optimization Services
Synoptek's IT Cost Optimization Services include overall IT cost-transformation services that provide a complete review of all technology services and the costs associated with operating those services. By scrutinizing the business needs, the use of technology, and the costs of supporting those technologies, Synoptek can save companies between 15% and 25% of annual IT costs.- Conduct initial planning that includes establishing timeframes, documenting scope, and confirming business and IT objectives
- Perform a preliminary IT security audit
- Identify important assets and determining the level of acceptable risk
- Incorporate IT security standards into your business plan
- Organize regular, in-depth information-gathering sessions
- Define and designing critical elements of an IT security policy
- Define responsibilities and roles for the team
- Create Network and Security Topological Architecture diagrams
- Define policies and procedures for remote access
- Manage compliance
- Manage risks
- Measure security provided by a third party
- Define and evaluate processes of security operations
- Train security personnel
- Create Security Response Plan and ensure:
- Security of applications
- Security of systems
- Security of networks
How can CISO as a Service Help Your Organization?
CISO as a Service works with your company on a regular basis to assist:- Creation and implementation of policies and processes in the areas of security, compliance, and governance
- Development and maintenance of an enterprise-wide vision, strategy, and best practices guaranteeing that their information assets and technologies are well protected
- Lead your IT team in identifying, designing, implementing, and maintaining processes throughout the company to conduct real-time threat analysis and execute remediation actions to mitigate the likelihood and impact of IT risks
- Conduct a gap analysis against existing frameworks (ITIL / COBIT / NIST / ISO 27001) as well to provide the groundwork for improved governance, risk management, and compliance supervision
The Challenges to Using CISO as a Service?
The biggest challenge to using CISO as a Service is finding the right Managed Services Provider (MSP) that has the experience in providing this service to organizations of all sizes successfully. The service must be designed in a manner that it acts as an extension of the organization's strategic leadership. Not many MSPs come with the relevant experience or ability to provide this service at scale.CISO as a Service from Synoptek
As an MSP, Synoptek delivers CISO services to help enterprises establish and maintain the best practices to ensure that their information assets and technologies are thoroughly protected. Our team of qualified vCISO consultants helps customers control risks to their infrastructure and assets. Synoptek experts bring years of experience in the relevant domain and help clients across the globe strengthen their security strategies and reinforce their security footing every day. With Synoptek's vCISOs, you will never feel the need for in-house security advisories. You will receive timely and detailed guidance to reduce exposure to the ever-growing threat landscape while also actively managing the potential impact of an incident in your enterprise ecosystem.Virtual CIO (vCIO) services provide strategic IT leadership and consulting to businesses, typically small and medium-sized enterprises (SMEs), by a remote, part-time Chief Information Officer. vCIOs offer executive-level expertise in aligning technology with business goals, optimizing IT investments, and driving operational efficiency.
How do Virtual CIO Consulting Services Differ from Traditional CIO Roles?
Unlike a full-time, in-house CIO, a virtual CIO operates as an independent contractor or through a managed service provider (MSP). This model offers more flexibility and cost-effectiveness, as businesses can access high-level IT strategy without the financial burden of a permanent executive-level position.
What Services do Virtual CIO Managed Services Typically Include?
Virtual CIO managed services often encompass a wide range of IT strategy and management tasks, such as:- Developing and implementing long-term IT strategies aligned with business objectives
- Budgeting and managing IT expenditures
- Overseeing cybersecurity measures to protect sensitive data
- Selecting and managing technology vendors and service providers
- Creating technology roadmaps to guide future investments
What are the Benefits of Working with a Virtual Chief Information Officer?
Engaging a virtual chief information officer, typically through a managed services provider, can deliver several benefits to businesses, including:
- Cost savings compared to hiring a full-time CIO
- Access to expert-level IT strategy and guidance
- Improved IT efficiency and alignment with business goals
- Proactive recommendations for leveraging emerging technologies
- Streamlined vendor management and contract negotiations
What Industries Benefit Most from vCIO Services?
vCIO (Virtual Chief Information Officer) services provide strategic IT leadership and consulting tailored to various industries. Here are the key sectors that benefit most from these services:
- Healthcare: With stringent regulations and the need for robust data security, healthcare organizations can leverage vCIO services to ensure compliance and protect sensitive patient information.
- Manufacturing: vCIOs help manufacturing companies optimize their technology infrastructure, improve operational efficiency, and implement automation solutions that drive productivity.
- Professional Services: Firms in consulting, legal, and accounting benefit from vCIO services by aligning their IT strategies with business objectives and enhancing data management practices.
- Nonprofits: Nonprofit organizations often face budget constraints, and vCIO services provide them with access to strategic IT leadership without the costs associated with a full-time CIO.
- Education: Educational institutions can use vCIO services to implement technology that supports learning, manages data security, and ensures compliance with educational regulations.
Are you looking to engage with a virtual CIO in Orange County? As an award-winning, globally trusted technology consulting and managed service provider (MSP) in Orange County, we offer a comprehensive range of virtual CIO services. Contact our vCIO experts in Orange County to learn more.
Get In Touch