April 16, 2020 · by Synoptek Team 6 min read
COVID-19 has transformed how businesses operate. In the last few months, as more and more companies have advised their employees to work-from-home, there has been a massive surge in demand for teleconferencing and remote collaboration tools. A work setup that facilitates remote collaboration and real-time communication is an immediate necessity for business continuity in the current situation, and therefore, organizations must optimize their existing setup to cater to the new, unanticipated needs. A non-optimized remote work setup not only affects collaboration and productivity but also poses a considerable security risk.
Security threats for collaboration platforms are real
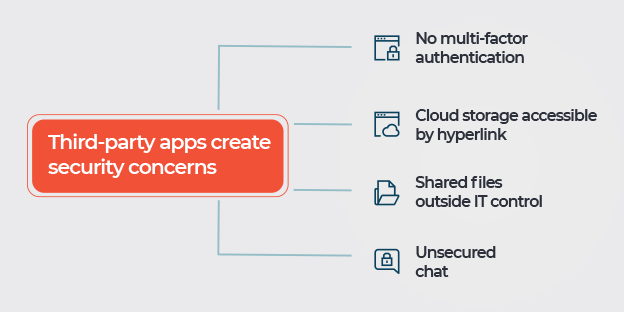
There have been incidents in the recent past that have brought to the fore-front significant vulnerabilities in two very popular collaboration/conference tools. Vulnerabilities in one of the tools could have potentially led to automated account takeovers (ATOs) and data breaches, while the other product had serious loopholes in its security and privacy posture. As these tools often interact with organizations’ critical assets and data, owing to the exchange of files and information via them, cybercriminals have been targeting these tools to exploit their weaknesses and vulnerabilities.
Access to critical data by unwanted parties due to these security loopholes can have serious business implications. In order to avoid a security incident, especially in the given scenario, organizations must aim to fully optimize their remote work setup with the right controls, policies, and processes.
Security and privacy are two uncompromisable aspects
While the need for rapid implementation of enterprise-level remote collaboration setup is non-negotiable in the current scenario, it is equally important to choose the right tool and right implementation partner for this critical exercise. The two key aspects that enterprises must focus on while selecting the tool, as well as the right implementation partner, is their emphasis on security and confidentiality.
When it comes to remote work setup – ‘Security’ means establishing ‘Zero Trust’ and ensuring ‘Confidentiality’
The most critical aspect when it comes to data security in a remote work setup is to ensure there is no data leakage (intentional or unintentional). This aspect becomes critical because more often than not data leakage is caused due to issues beyond the collaboration tool’s breach. Users, when working in a remote setup, engage in risky behavior to simply get their job done – for example accessing, editing, and sending an official document using a home laptop, which could potentially be infected with malware.
According to the 2017 State of Endpoint Security Risk Report, 54% of companies experience breaches that compromise data and/or IT infrastructure – out of these breaches about 51% are initiated through the remote log-in entry points.
Therefore, to avoid security compromises, a remote work setup should be designed on the “Zero Trust” tenet. The “Zero Trust” tenet means that from the start, no action is trusted. The Zero Trust model provides a higher level of security by looking beyond passwords and authentication and bringing in a tighter security framework, which is designed around the user behavior and is supplemented by added layers of security such as a Virtual Private Network (VPN), Multi-factor Authentication (MFA), and/or conditional access rules to ensure network traffic is trusted by corporate network security standards.
Another critical security aspect in a remote work setup is to maintain the integrity of data. Data can be accessed, deleted, and worse – changed by someone who shouldn’t have access to the data in the first place. And note, it’s not enough to protect the data in transit or in the backend, but also in the device itself. That’s why in a remote work setup, securing the endpoint is also extremely important.
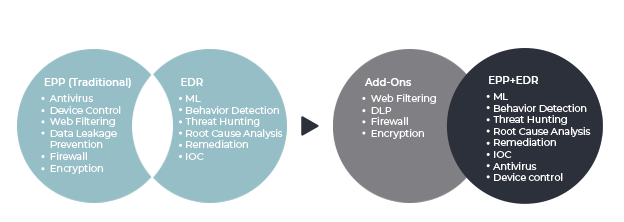
For comprehensive protection, endpoints need to be safeguarded beyond traditional Endpoint Protection Platforms (EPP). Organizations now need a Unified Endpoint Security (UES) solution that encompasses EPP + Endpoint Detection and Response (EDR) solutions along with encryption and firewall (perimeter security) as add on capabilities that complement UES.
Confidentiality is another critical factor for both security and compliance requirements. Confidentiality measures ensure that sensitive information is delivered to the people who are authorized to have access to it. The confidentiality factor can’t be simply tool-driven; it also needs strict policy controls that can be leveraged in conjunction with the remote collaboration tool’s capability. For example, we can conditionally grant unique roles access to sensitive data under “Least Privilege” design. For needs related to compliance, we can configure a data retention policy to store the chat history in Microsoft Teams for one year or more.
Security controls must be tailored to suit the company’s ecosystem
Security controls ensure that employee behavior is predictable and sensitive company data is protected by executive approved policies. It also encourages accountability among the remote workforce as they become more aware of how and when to access company data.
However, in order to create such a work setup, organizations need a strategic advisor like Synoptek that understands the company’s business objectives and then tailors the security controls, policies, and processes according to the company’s needs and targeted towards their customer risk scenarios regarding data, communication, and IP while not hindering productivity.
If you are looking for a secure and scalable remote work setup tailored for your company – explore Synoptek’s Teamwork as a Service offering
Synoptek’s new offering, Teamwork as a Service, is exclusively designed keeping in mind the data security, collaboration, and productivity aspects for creating a successful remote workforce in the current scenario. This service offering intends to help enterprises achieve productivity objectives of the workforce using Microsoft Teams. The offering empowers enterprises to effectively as well as securely collaborate using tailored confidentiality (privacy) policy design, collaboration design, and strategic advisory and governance against business outcomes.
Provided as a standalone or complementary service to Synoptek’s End User Management services, the offering, apart from ensuring data security in remote work setup, enables efficient collaboration, timely document management, and seamless user access and control while greatly minimizing time-to-decision for the enterprise workforce. When enabled with new digital workplace applications, workforces have shown effective delivery in less time.
The standard components of the offering not only comprise designing a “Least Privilege” user access policy, organizational design for document collaboration, help with call quality problems, but also include regular executive review and governance to ensure business productivity objectives and Microsoft Teams adoption levels are hitting KPIs.
To learn more about Teams as a Service offering, download this datasheet and read this blog.
